Demonstrate an understanding of potential risks to a unit.

MONITOR, ASSESS AND MANAGE RISK
There are many definitions and types of “risk’, but for the purposes of this module we will focus on risk in our business unit and say that “risk is anything that threatens the ability of an organisation or business unit to accomplish its goals”.
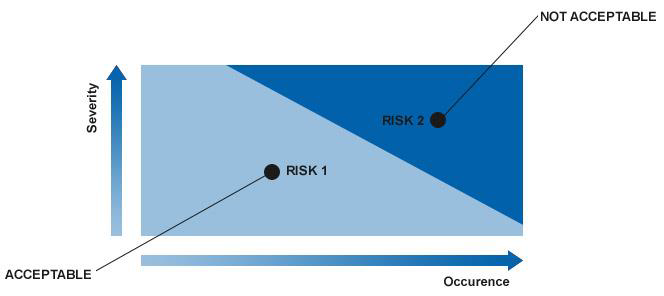
Risk is defined as the combination of the probability of occurrence of harm and the severity of that harm.
Severity is associated to a potential failure effect and indicates the related seriousness.
Occurrence is related to the causes of a potential failure mode and corresponds to the estimate of the number of failures that could occur. Hazard is a potential source of harm (physical injury to the health of people, damage to the property or to the environment).
Risk Management is the process of measuring, or assessing risk and then developing strategies to manage the risk. Risk management is a discipline for dealing with uncertainty. It enables people and organisations to cope with uncertainty by taking steps to protect vital assets and resources.
Risk Management is a systematic and structured decision-making process, focused on value creation, able to identify, assess and prioritise risks throughout the product life cycle.
Every organisation faces uncertainty and risk. Few, if any, operate in risk-free environments. From uncertainty about economic indicators to concerns about safety and the organisation’s ability to retain client support, managing a range of risks is required for both survival and success. Every organisation – even very small ones – can use risk management strategies and tools to protect vital assets.
Risk Management is about identifying and analysing the things that may have a major effect on your business and choosing the best method of dealing with each risk. By developing a Risk Management Plan you ensure your business risks are managed.
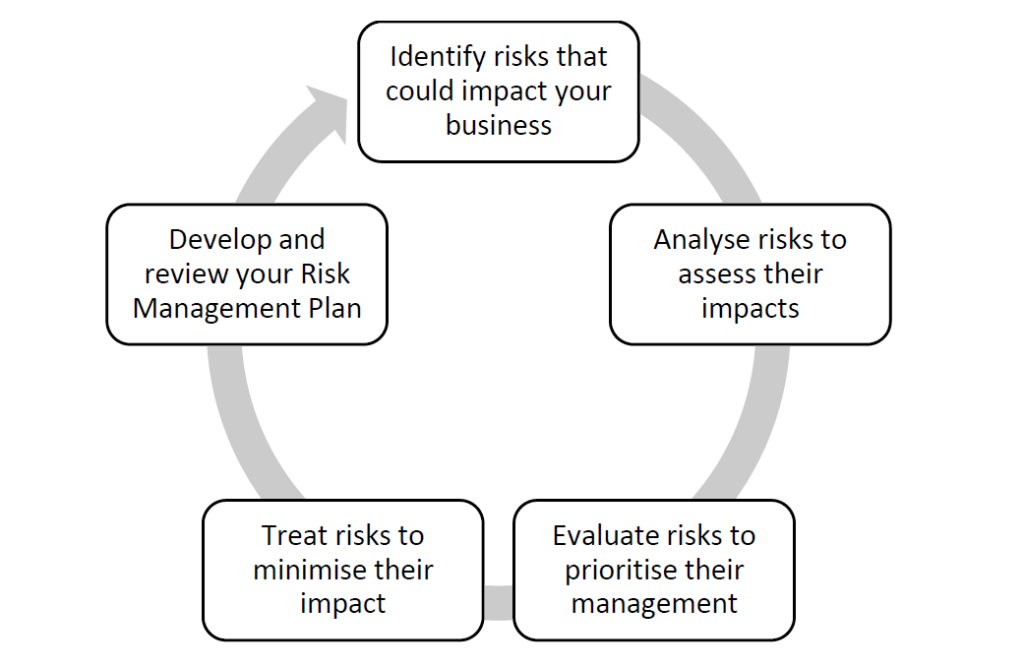
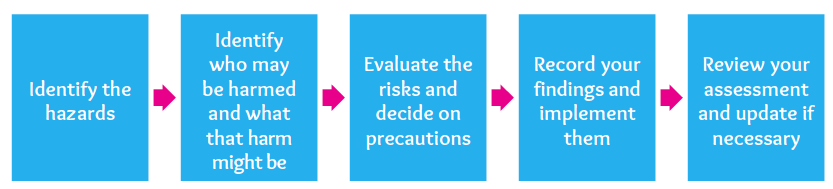
The process of managing risks involves five steps:
Step 1: Identify risks that could impact your business:
Take a close look at each of your business operations and ask yourself:
What could have an impact?
How serious would that impact be?
What is the likelihood of this occurring?
Can it be reduced or eliminated?
For example, if you owned a cafe, your risks might include fire, food poisoning and floods (if you are located in a flood-prone area).
Step 2: Analyse risks to assess their impacts
Determine which risks have a greater consequence or impact than others. Separate minor acceptable risks from major risks which must be managed immediately. This involves deciding on the relationship between the likelihood and impact of the risks you have identified.
In a cafe, the likelihood of a flood may be assessed as low, but the impact on the business would be very high. A flood could potentially destroy both equipment and stock and would lead to loss of trade and financial loss.
Step 3: Evaluate risks to prioritise their management
Compare the likelihood and impact of each risk to evaluate and prioritise the resources you are prepared to invest to treat these risks. The outcome of this step is a prioritised list of risks that require further action.
In the cafe example, your prioritised list may be:
Fire – your top priority risk. The likelihood is high and the potential impact of a fire on the business is very high.
Food poisoning – your second priority risk. Whilst the probability may be assessed as low, the impact on the business would be very high.
Flood – your third priority risk. The probability is assessed as very low, but again the impact on the business would be very high.
Step 4: Treat risks to minimise their impact
You will need to determine which risks are acceptable for your business to leave untreated and which risks need to be treated.
Risk treatment is about considering options for treating risks that are not considered acceptable, through a number of strategies including:
insurance
quality control processes
staff training
complying with government legislation and regulations
properly maintaining facilities, plant and equipment
using appropriate security devices
establishing systems and controls, e.g. segregation of duties (cash receipting, banking and accounting)
developing contingency plans.
Some of the treatment strategies for the risk of flood might include:
ensure flooding is covered by your existing insurance policy and the amount of cover is adequate
ensure stock and equipment are stored off the ground where possible
organise off-site storage for stock and equipment when a flood is forecast.
Step 5: Develop and review your Risk Management Plan
A Risk Management Plan indicates the chosen strategy for treatment of the identified risks. It details information about:
risks identified
level of risks
planned strategy
timeframe for implementing the strategy
resources required
individuals responsible for ensuring the strategy is implemented.
The final documentation should include appropriate objectives, a budget and milestones on the way to achieving those objectives.
Benefits of Risk Management
There are a number of benefits to having a solid risk management process, including:
Clear ownership and accountability for all risks
Creation of an environment where risks will be accepted by the business on an informed basis
An increased likelihood that the program will be a success, along with the increased likelihood that the objectives of the organisation will be met.
The discipline of risk management helps identify, assess and control risks that may be present in operations, service delivery, staffing, and governance activities. It is well worth the time to integrate risk management into your operations and there are many good reasons to do so:
The threat of litigation is increasing – Many organisations may never face a lawsuit, but those that do, know that it can be costly and time consuming. Good risk management can reduce these costs or perhaps help you to avoid a lawsuit altogether.
The risk of client/ staff harm – Your mission is to help people, not hurt them. Causing harm to a client, however unintentional, undermines your purpose and jeopardises your mission.
For your own safety and security – Sound risk management will help create a sense of confidence and safety about your operation. In an atmosphere where the threat of unnecessary risk is reduced, an organisation can be more creative in providing services to clients and achieving results.
The risks of not applying timeous and proper risk management are:
Not eliminating faulty practices
Reinforcing faulty practices
Blocking experimentation
Not encouraging experimentation
Blocking technical improvements
Not encouraging technical improvements.
Prioritising too highly the risk management process itself could potentially keep an organisation from ever completing a project or even getting started. This is especially true if other work is suspended until the risk management process is considered complete.
In general, the strategies employed in risk management include transferring the risk to another party, avoiding the risk, reducing the negative effect of the risk, and accepting some or all of the consequences of a particular risk. These will be discussed in more detail later.
Traditional risk management
Traditional risk management focuses on risks stemming from physical or legal causes (e.g. natural disasters or fires, accidents, death, and lawsuits).
Financial risk management
Financial risk management, on the other hand, focuses on risks that can be managed using traded financial instruments.
Intangible risk management
Intangible risk management focuses on the risks associated with human capital, such as knowledge risk, relationship risk, and process – engagement risk.
Knowledge risk occurs when deficient knowledge is applied.
Relationship risk occurs when collaboration ineffectiveness occurs.
Process-engagement risk occurs when operational ineffectiveness occurs.
These risks:
Reduce the productivity of knowledge workers
Decrease cost effectiveness
Reduce profitability
Impair service
Reduce quality
Damage reputation and brand value
Reduce earnings quality.
Intangible risk management allows risk management to create immediate value from the identification and reduction of risks that reduce productivity.
Regardless of the type of risk management, all large corporations have risk management teams and small groups and corporations practise informal, if not formal, risk management.
In the ideal risk management scenario, a prioritisation process is followed whereby the risks with the greatest loss and the greatest probability of occurring are handled first, and risks with lower probability of occurrence and lower loss are handled later.
In practice, the process can be very difficult, and balancing between risks with a high probability of occurrence, but lower loss vs. a risk with high loss, but lower probability of occurrence can often be mishandled.
Risk management also faces a difficulty in allocating resources properly. This refers to the concept of opportunity cost. Resources spent on risk management could instead be spent on more profitable activities. Again, the ideal risk management scenario entails spending the least amount of resources on the process of managing risks, while reducing the negative effects of the risks as much as possible.
Demonstrate an understanding of potential risks to a unit
Risk is exposure to loss as a consequence of uncertainty. The impact of risk can be measured by the likelihood of an unwanted event occurring and the consequences if it does occur. For planning purposes, the impact of risk could be the same for both small damage resulting from a highly probable recurring event and very large damage resulting from a rare event.
Concept of Risk
Risk can be defined as “the potential impact (positive or negative) to an asset or some characteristic of value that may arise from some present process or from some future event”.
Risk – The probable frequency and probable magnitude of future loss
There are three important things to recognise from this definition:
First and most obvious – risk is a probability issue. We’ll cover this in more detail throughout the learner guide.
Second – risk has both a frequency and a magnitude component.
And third – is that this definition for risk applies equally well regardless of whether we’re talking about investment, market, credit, legal, insurance, or any of the other risk domains (including information risk) that are commonly dealt with in business, government and life. In other words, the fundamental nature of risk is universal, regardless of context.
In everyday usage, “risk” is often used synonymously with “probability” and restricted to negative risk or threat.
In professional risk assessments, risk combines the probability of an event occurring with the impact that event would have.
Risks can be defined as many things, but at the root of every definition is the fact that risks represent uncertain outcomes. These outcomes can be either negative or positive. They can represent positive opportunities (opportunities for excellence), as well as negative threats.
Types of Risk
Upside risk
An upside risk is something that might happen that’s better than some benchmark level. The benchmark is something we choose, but typically it is our planned or expected outcome, or the outcome we think ‘ought’ to happen.
In some areas of risk management the upside is more important than in others. In safety, for example, the natural benchmark is ‘total safety’ (one does not want to speculate about how many people one ‘expected’ or ‘planned’ to kill or injure.) Consequently there is no upside to speak of.
By contrast, in financial risk management it is natural to talk about expected returns and there’s nearly always an important upside to consider.41
Positive risk refers to risk that we initiate ourselves because we see a potential opportunity, along with a potential for failure. We have to be intelligent risk takers. For example, we have a project that is scheduled to take 90 days to complete. The client would rather the project be delivered earlier, and would get more value if it were delivered earlier, but understands that 90 days is how long the project will take. One of your team members has an idea: If you utilise a new machine, it’s possible that you can deliver the project in 60 days instead of 90. If this were a guaranteed solution, you would jump on it. However, there is risk, since it will be the first time you’ve used the machine. You have to deal with a lack of expertise and a learning curve. It’s possible that if the machine doesn’t work out, the project could end up taking 110 days to deliver. What would you do?
Downside risk
The risk that an asset will decline in value, including the implications of risk, e.g. a “worst case” scenario of the gradation of risk in which an investor will lose money in a business venture if the venture fails.
Negative risk is represented by potential events that could harm a project. In general, these risks are to be avoided, e.g. you have a supplier that you’re counting on to provide raw materials to build a prototype. The supplier has a union contract that expires in the next 60 days. There is a risk that the supplier will have a strike that will disrupt shipments. You need to identify this as a risk, estimate the probability of occurrence (perhaps this will increase or decrease over time), determine the impact to the build if it occurs, and then put together a plan to minimise the impact on the project if it occurs
Example:
The implications of meeting and exceeding or not meeting quality requirements are also referred to as upside and downside risk.
Upside risk is the potential gain for both the individual and the company if standards are met and exceeded.
Downside risk is the potential loss both the individual and the organisation may suffer if quality standards are not met.
The following examples will help you gain a better understanding of the upside and downside risks of the outputs of a job:
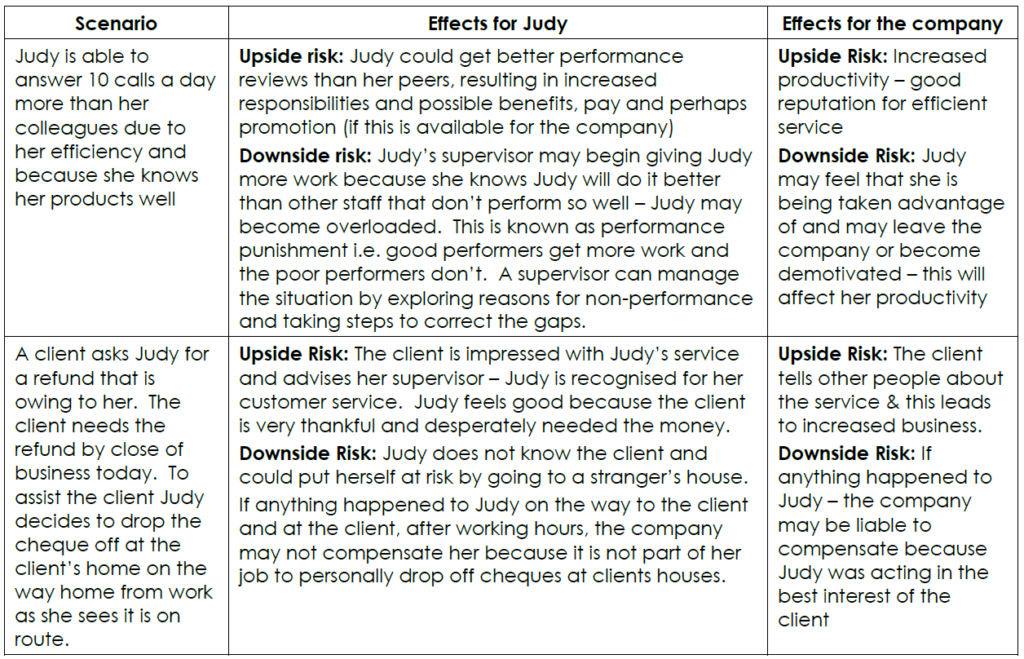
When outputs are produced according to quality requirements the employee, company and customers benefit. The business stays profitable and attracts more customers.
When outputs are not produced according to quality requirements, a lot of time is wasted fixing up errors, re-doing work which ultimately costs money and could even result in the business having to close down, customers being dissatisfied, employees being dismissed for poor ratings, etc. There is always a price to pay for not doing the job correctly.
Categories of Risk
There are many examples of risk in business. To identify your specific business risks, consider them in categories.
The link between RISK and LOSS is obvious – and it has produced during the past 50 years a group of specialised activities all devoted to reducing loss. Ironically – though each “petal of the RISK flower42” attempts to minimise corporate loss. Further, they are unaccountable for the resources management invests in them. Not one of them can provide “dollars saved per dollar invested.”
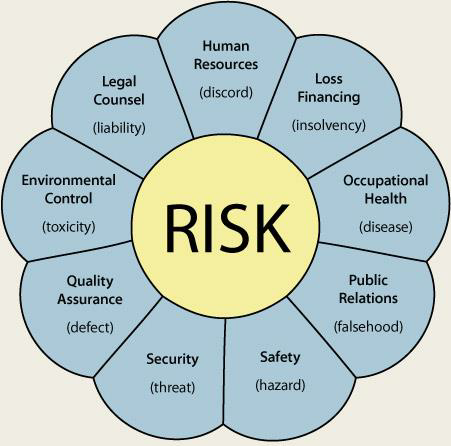
Risk categories should be considered one by one, providing a structured approach to risk identification. This enables greater focus on a particular category, stimulating thought, and increasing the opportunity of identifying a broader range of risks.
Common risk categories are:
Financial – includes cash flow, budgetary requirements, tax obligations, creditor and debtor management, remuneration and other general account management concerns.
Equipment – extends to equipment used to conduct the business and includes everyday use, maintenance, depreciation, theft, safety and upgrades.
Organisational – relates to the internal requirements of a business, extending to the cultural, structural and human resources of the business.
Security – includes the business premises, assets and people. Also extends to security of company information, intellectual property, and technology.
Legal and regulatory compliance – includes legislation, regulations, standards, codes of practice and contractual requirements. Also extends to compliance with additional ‘rules’ such as policies, procedures or expectations, which may be set by contracts, customers or the social environment.
Reputation – entails the threat to the reputation of the business due to the conduct of the entity as a whole, the viability of products/services, or the conduct of employees or others associated with the business.
Operational – covers the planning, daily operational activities, resources (including people) and support required within a business that results in the successful development and delivery of products/services.
Contractual – meeting obligations required in a contract including delivery, product/service quality, guarantees/warranties, insurance and other statutory requirements, non-performance.
Service delivery – relates to the delivery of services, including the quality of service provided, or the manner in which a product is delivered. Includes customer interaction and after-sales service.
Commercial – includes risks associated with market placement, business growth, product development, diversification and commercial success. Also to the commercial viability of products/services, extending through establishment, retention, growth of a customer base and return.
Project – includes the management of equipment, finances, resources, technology, timeframes and people involved in the management of projects. Extends to internal operational projects, business development and external projects such as those undertaken for clients.
Safety – including everyone associated with the business: individual, workplace and public safety. Also applies to the safety of products/services delivered by the business.
Workplace safety – Every business has a duty of care underpinned by legislation. This means that all reasonable steps must be taken to protect the health and safety of everyone at the workplace. Occupational health and safety is integrated with the overall risk management strategy to ensure that risks and hazards are always identified and reported. Measures must also be taken to reduce exposure to the risks as far as possible.
Stakeholder management – includes identifying, establishing and maintaining the right relationships with both internal and external stakeholders.
Client-customer relationship – potential loss of clients due to internal and external factors.
Strategic – includes the planning, scoping, resourcing and growth of the business.
Technology – includes the implementation, management, maintenance and upgrades associated with technology. Extends to recognising critical IT infrastructure and loss of a particular service/function for an extended period of time. It further takes into account the need and cost benefit associated with technology as part of a business development strategy.
Knowing your risk categories can assist you in risk planning and communicating risk information. They provide a structure for identifying risk and are often initially identified through a brainstorming exercise.
Factors that could constitute Risks to a Unit
The risks facing an organisation and its operations can result from factors both external and internal to the organisation. The risks can be categorised into types of risk such as strategic, financial, operational, hazard, etc.
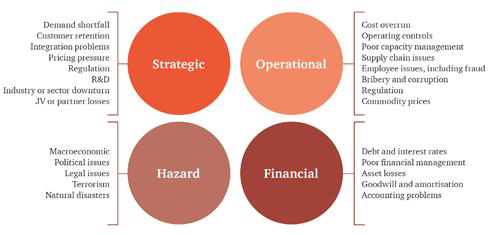
Financial risks are typically well controlled and are part of the routine focus of management risk discussions, with increased regulatory, accounting and financial audit focus. As financial information is a key element of stakeholder communications, performance measurement and strategic delivery, management risk discussions will devote considerable time to these risks. Financial risk is often defined as the unexpected variability or volatility of returns, and includes both potential worse than expected as well as better than expected returns. We know that organisations require a steady stream of reliable income in order to operate and grow
Operational risks are typically managed from within the business and often focus on health and safety issues where industry regulations and standards require. These internally driven risks may affect your organisation’s ability to deliver on its strategic objectives.
Hazard risks often stem from major exogenous43 factors, which affect the environment in which the organisation operates. A focus on the use of insurance and appropriate contingency planning will help address some of these. However, there is often a danger that as many of these risks cannot be controlled, boards and senior management will not reflect these in their strategic thinking. Confining strategic management to controllable factors will leave your business at risk of failing to address these factors.
Strategic risks are typically external or affect the most senior management decisions. As such, they are often missed from many risk registers. Your senior management has a responsibility to make sure all these types of risks are included in their key strategic discussions.
Asset Risk
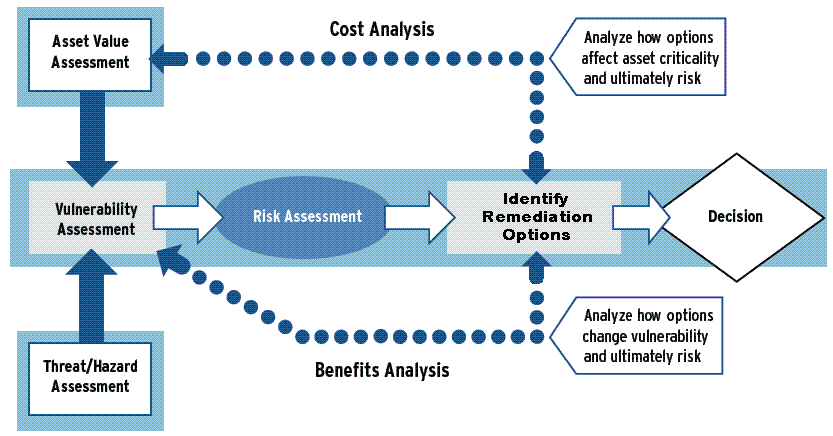
Some organisations prefer to look at factors related to asset when identifying factors that could constitute risks to a unit.
We can categorise asset risk according to four major categories of assets:
Property risk – Property includes:
o Buildings
o Office furniture and fixtures
o Computers (hardware and software)
o Intellectual property (trademark, logo, copyright, patent, etc.)
o Motor vehicles
o Other equipment (lawn maintenance equipment, contractors’ equipment, audio-visual equipment, laptops, exhibits, etc.)
Property also includes cash and securities, financial assets and even borrowed property. Property risks come in various forms, including those caused by nature (flood, earthquake, hurricane, forest fires, wind/tornadoes, extreme heat or cold) and others resulting from human intervention (fire, theft, vandalism, collision, carelessness). The risks of loss associated with property and income assets could devastate an organisation. Imagine what would happen if your organisation’s computers and accounting records were lost in a fire, or if a significant sum of money were embezzled.
Income risk – Depending on the type of organisation, common sources of income include:
o Donations
o Grants
o Government contracts
o Fees for services
o Investment income
o Merchandise sales
o Loans
o Proceeds from special events
o Sponsorship fees
o Registration/ participation fees
o Membership dues
Most managers have come face to face with an income risk, such as the loss of budget, sales falling shy of projections, contract cancellations and more. A disaster such as a fire or flood can also curtail operations, resulting in an interruption of the income stream. Consequences of a loss can range from inconvenience to devastation. While income ups and downs are arguably part and parcel of the business world, it’s possible to use risk management techniques to reduce the likelihood that a loss of income will destroy an organisation.
Some techniques for reducing income risk include:
o Business interruption insurance
o Establishing a reserve fund
o Implementing sound financial controls
o Diversifying income sources
Goodwill risk – Goodwill is an asset that is difficult, if not impossible, to quantify. A more descriptive word might be “reputation.” Every organisation understands that its reputation is key to recruitment of staff and customers, retention of those staff and customers, and overall good organisational health. Damage to reputation can be devastating, and many organisations would have a hard time recovering from a blow to their reputation. In many cases, damage to reputation occurs in the wake of a crisis, such as a scandal involving maladministration or widely publicised client injury. In some cases there may be guilt by association if a corporate partner comes under fire. Even an incident of tax evasion by a major shareholder could have repercussions for an organisation
Operational risk – Operational risk is defined as the risk of loss resulting from inadequate or failed internal processes, people and systems, or from external events.
Examples of operational risk include:
o Technology failure
o Business premises becoming unavailable
o Inadequate document retention or record-keeping
o Poor management
o Lack of supervision
o Lack of accountability
o Poor control
o Errors in financial models and reports
o Attempts to conceal losses
o Attempts to make personal gains
o Third party fraud
A delict is an act (or omission) which in a wrongful and culpable way causes loss to another – responsibility toward society at large. This is where potential losses are most difficult to estimate. You may have heard of the Thalidomide disaster. In the 1960’s a drug meant to relieve morning-sickness in pregnancy resulted in babies being born deformed. It is thought that a similar disaster under today’s conditions could result in awards as high as R5bn. (This is an example of Products Liability).
A boiler explosion might cause tremendous physical damage, and interrupt production, but the liability claims for physical injury and damage to third party property can be even bigger.
An organisation can suffer loss even without legal liability being established:
o The cost of investigation, and documenting their defence;
o Legal fees;
o Out of court settlements, where it is considered more cost effective to settle with the claimant, than risk everything on the outcome of an expensive court action.
o Where disputes actually go to court, legal costs are much greater, as are the actual awards handed down.
People risk – People are the heart and soul of an organisation. They represent the talent, commitment and community your organisation serves. The people assets in your organisation include staff, clients and shareholders.
Examples of people risk include:
o Risk of Staff Loss: Each person is a unique individual with a unique set of skills. In a very real sense, each is irreplaceable. So the first risk in terms of employees is the risk of loss of talent/ expertise when a trained and skilled employee leaves the organisation.
o Health and safety: Another risk is that of loss due to injury or death. Unlike damage to property or loss of income, injuries sustained by employees may never be fully repaired and could lead to expensive litigation. In the workplace, an organisation’s priority must be the health and safety of all. The goal is the prevention of occupational health risks, accidents and injury. This means that all must work to legal health and safety standards and improve on these wherever possible. All employees must constantly be on the alert against possible hazards and hazardous behaviour. The organisation must minimise such hazards with well-designed procedures, processes, equipment and safety training programmes. The organisation must ensure that all employees are aware that irresponsible or careless activities place themselves and others at risk.
o Employee turnover: In terms of employee decision-making, Andrew Wong44 says it is natural for an employee to aspire to earn a better salary. Financial gain not only helps to meet the financial needs and improve the lifestyle of the person and his/her family, it may also reflect greater capability of the employee to take up greater scope of work or responsibilities. An opportunity may arise whereby there is a significant financial gain (e.g. higher salary, or allowances or both), but with higher occupational hazards, or perhaps s/he has an opportunity to work in a foreign country which has security risks, or entails harsh living conditions for the employee and the family. Of course, each person has his or her own tolerance level with respect to the above-mentioned risks. Rationally and emotionally, he or she will make decisions based on certain criteria, making the necessary evaluation and assessment. The general rationale is “suffer a few years for that extra significant financial gain” and this then becomes the governing principle or reason to make the decision to take up a new job or transferred position. However, in the scenario described by Wong, there is also a significant risk to the organisation: if the employee perceives the payoff to be “not worth it” after a while and cannot handle the increased workload or strain, s/he can become demotivated and unproductive, even though it was his/her own choice. That is why organisations have Wellness or Employee Assistance Programmes (EAP) in order identify, interact with and refer troubled employees before they affect productivity and team morale.
o At Risk Behaviour: As a manager, you will be held accountable for your subordinates’ behaviour – good or bad. You can take a proactive approach to eliminating at risk behaviour by recognising its causes in the workplace. The possible sources of at risk behaviour are endless and will vary on its degree of severity and the impact it will have on the performance of your team. Some sources of at risk behaviour could relate to the following:
Ignorance – Ignorance could create at-risk behaviour when your subordinates don’t know all they should about a situation. As a result, they might not be able to recognise, diagnose, or fix a dilemma. You should make sure that your subordinates are educated about your company and its current activities, goals, vision, values policies and procedures. By training your employees on these issues you could pro-actively avoid future high risk situations.
Lack of recognition by management – Recognition by management is an important form of reward for an employee. If a manager does not recognise an employee who needs recognition, the employee can become frustrated and might change his/her behaviour patterns to gain the manager’s attention. Although this attention could be negative, the employee would rather be recognised this way than not at all, e.g. an employee might start coming in late regularly or fail to submit reports or start to verbally abuse others, simply to get attention. This could in the long term impact negatively on conduct, productivity, performance and capacity.
Personal financial burdens – When an employee does not earn enough money to cover personal expenses, he might become a high risk, especially if he/she works with money. In this instance at risk behaviour can have two objectives: to take revenge on the organisation, or to obtain enough money to cover their personal expenses. As a manager, you might have the authority to determine salary levels for your subordinates. It is unrealistic for managers to grant subordinates all the salary they might want. Yet it is realistic to pay employees a salary based on industry standards. If your organisation’s salary levels fall below such standards, you can expect to encounter at risk behaviour.
Substance Abuse – This includes drugs and alcohol and has, in recent years become a serious social and business problem. The substance abuser poses a major threat to an organisation in terms of productivity, performance and conduct. The condition is often not apparent but manifests itself with poor performance issues, absenteeism and financial burdens.
o Environmental and Corporate Social Responsibility: Outside of the workplace, an organisation’s priority must be to act responsibly by protecting the environment and the communities around it. In addition, organisations must ensure that they act responsibly at all times in the disposal of waste and in pollution control.
Acts and Regulations related to Risk Management
In terms of the South African Compensation for Occupational Injuries and Disease Act, applicable to most classes of employees, automatic compensation is paid from a state administered fund. This relieves employees from having to prove negligence by the employer, but also means that they cannot sue the employer.
This does not free the employer of the need to take suitable precautions.
Requirements have been laid down, some of the principal statutes being:
The Occupational Health and Safety Act No 85 of 1993 (as amended)
The Mines and Works Act No 27 of 1956 (as amended)
The Electricity Act No 40 of 1958 (as amended)
all as read in conjunction with the Criminal Procedure Act No 51 of 1977 (as amended).
Failure to meet these requirements will result in criminal action against the person responsible. Special audit sheets are needed to check that the requirements are met.
Note: These are also regulations relating to specific trades and types of hazard.
Role of Organisational Policies and Procedures
Quality standards are defined in terms of company, legislation or industry standards. Company policies and procedures are developed as a result of interpreting industry standards and/or legislation. The company policies and procedures form part of the risk management process in that they provide guidelines to ensure that the company adheres to industry standards and Statutory Requirements, e.g. Acts, Bills
Regulatory Requirements, e.g. Regulations, Rules
Supervisory Requirements, e.g. Directives, Codes, Standards, Procedures, Rulings
Company codes, policies and procedures
Risk Management Policy
An organisation’s risk management policy should set out its approach to and appetite for risk and its approach to risk management. The policy should also set out responsibilities for risk management throughout the organisation.
Furthermore, it should refer to any legal requirements for policy statements e.g. for Health and Safety.
Attached to the risk management process is an integrated set of tools and techniques for use in the various stages of the business process. To work effectively, the risk management process requires:
commitment from the chief executive and executive management of the organisation
assignment of responsibilities within the organisation
allocation of appropriate resources for training and the development of an enhanced risk awareness by all stakeholders.
Quality Standards
Quality standards are the measurable quality requirements for each work responsibility or duty, often referred to as the output of your work.
Outputs are the products and services that individuals in an organisation provide to one another or to the customer, such as:
An answered telephone
A clean floor
A serviced car
A completed report
An issued policy document
A teamwork plan.
Listing responsibilities as outputs is useful, because there are many ways to produce an output even though the standards that need to be maintained are the same. By listing outputs you encourage a process of continuous improvement, because you create a certain amount of freedom, to the person producing the outputs, to experiment with different ways of doing the work in an attempt to improve the way the outputs are produced.
Example: The receptionist is required to answer the telephone within 3 rings in a polite professional manner.
As the standard has been set, the receptionist can now be measured accordingly.
The receptionist would have been informed why this is important (image of the company) and would now understand why she has to comply with the standard.
Quality standards provide guidelines in terms of requirements that need to be met to make sure that the outputs are produced according to set standards. Quality standards are often defined in terms of regulatory compliance, cost, time, quantity and quality.
The risk management process is the series of steps that enable initial and continual review of risk, and help to ensure that the business is on-track for meeting its objectives.
The risk management process helps to put in place and review the risk management plan.
The elements of the risk management process are:
establish the context
identify the risks
analyse the risks
evaluate the risks
treat the risks
monitor and review.
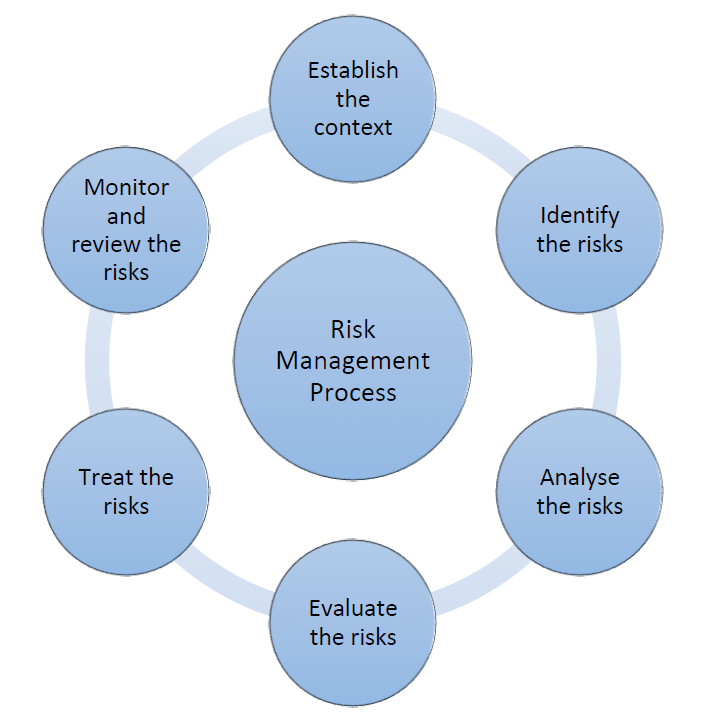
- Establish the context
When considering risk management within a small business, it is important to establish boundaries for the risk management process. For example, a business owner may be only interested in identifying financial risks so information collected will only cover that area of risk.
In establishing the context, consider:
the objectives of the business
key stakeholders and impacts
risk categories.
It is generally more productive to break down the risks into categories, rather than identify risks for the company as a whole. - Identify the risks
Risk cannot be managed unless it is identified. Once the context of the business has been defined, the next step is to use this information to identify as many risks as possible.
The aim is to identify the risks that may affect, either negatively or positively, the objectives of the business and all its activity.
Identify the range of hazards, threats, or perils that impact or might impact:
your organisation.
your infrastructure.
the surrounding area.
You will need to:
Identify retrospective risks – Retrospective risks are seen in incidents or accidents that have occurred in the past. Retrospective risk identification is the most common way to identify risk and the easiest. A risk is easier to understand if its impact has already been experienced. It is also easier to quantify its impact and to evaluate the damage. There are many sources of information about retrospective risk including:
o hazard or incident logs or audit reports
o customer complaints
o accreditation documents and reports
o staff or client surveys
o newspapers or professional media, such as journals and websites.
Identify prospective risk – Prospective risks are harder to identify. These are things that have not yet happened, but might happen in the future. Identification should cover all risks, whether or not they are currently managed. The plan will be to record all significant risks and monitor the effectiveness of their treatment. Methods for identifying prospective risks include:
o brainstorming with staff and external stakeholders
o researching the economic, political, legislative and operating environment
o interviewing staff and clients to identify potential problems
o flow charting a process
o reviewing system design or preparing system analysis.
Risk categories will help break down the process for prospective risk identification. It is important to remember that risk identification will be limited by the experience and perspective of those conducting the risk analysis. Problem areas and risks can be best identified by the use of reliable sources.
In addition, understanding categories assists business owners to select the best tools and techniques for risk identification and analysis. For example, if a particular risk category is technical in nature, the risk identification methodology used will involve significant research and collection of existing information about risk exposure.
- Analyse the risks
During risk identification, a business owner may have identified many risks but it is often not possible to address all of them.
Determine the potential impact of each hazard, threat, or peril by estimating the:
relative severity of each hazard, threat, or peril (danger).
relative frequency of each hazard, threat, or peril.
vulnerability to each hazard, threat, or peril of your people, your operations, your property, and your environment.
Risk analysis will determine which risks have a greater consequence. This will provide better understanding of the possible impact of a risk, and the likelihood of it occurring. That leads to decisions about resources required to control the risks.
Risk analysis involves combining the possible consequences, or impacts, of an event, with the likelihood of that event occurring. The result is called a ‘level of risk’.
Risk = consequence x likelihood.
The risk analysis should be documented in the risk management plan. - Evaluate the risks
It is important to determine how serious the risks facing a business are. The business owner must determine the level of risk that a business is willing to accept. Risk evaluation involves comparing the level of risk found in the analysis process with previously established risk criteria. From there it must be decided if these risks require treatment.
Categorise each hazard, threat, or peril according to how severe it is, how frequently it occurs, and how vulnerable you are.
The result of a risk evaluation is a prioritised list of risks that require further action. This step is about deciding whether risks are acceptable or need treatment.
Low or tolerable risks may be accepted. ‘Accepted’ means the business chooses to accept that the risk exists, either because the risk is low and the cost of treating it would be uneconomic, or there is no reasonable treatment that can be implemented.
A risk may be accepted if:
the cost of treatment exceeds the benefit, so that acceptance is the only option (applies particularly to low risks)
the level of the risk is so low that specific treatment is not called for
the opportunities presented outweigh the threat to such a degree that taking the risk is justified
there is no treatment for the risk – for example, the risk that the business may suffer storm damage.
If the risk is medium or high and therefore not acceptable, the risk must be mitigated or treated. Specific actions to treat the risk should be outlined in the risk management plan.
- Treat the risks
Risk treatment is about options for dealing with risks that are not acceptable. Risk treatment involves identifying controls for risk. The aim is to either reduce or eliminate negative consequences, or to reduce the likelihood of an adverse occurrence. Risk treatment should also enhance positive outcomes.
It is often not possible, nor cost-effective to implement all treatment strategies. A business owner should choose, prioritise and implement the best combination of risk treatments.
Develop strategies to deal with the most significant hazards, threats, or perils. Develop strategies (risk treatments) to:
prevent,
mitigate,
prepare for,
respond to, and
recover from hazards, threats, or perils that impact or might impact your organisation and its people, operations, property.
The steps to this are:
identify – develop and design treatment options
evaluate – do the options satisfy treatment objectives and are they cost effective?
develop and implement a risk treatments and controls.
For businesses, many of the treatments are often part of establishing everyday business practices and procedures such as:
staff training and development
financial reporting systems
good customer management
ensuring compliance.
Therefore, ensuring good management practices are already in place will help you control risks from the outset.
A quality assurance program can also help to control risk. Quality assurance is the process that continues from risk treatment through monitoring and review to a cycle of continuous improvement.
All risk treatments should be documented in your risk management plan.
- Monitor and review the risks
Monitoring is an essential step in the risk management process. A business owner / manager must monitor risks and review the effectiveness of treatments and strategies that have been set up to manage risk.
Risks need to be monitored regularly to ensure changing circumstances do not alter risk priorities. Very few risks are static, therefore the risk management process needs to be repeated often, so that new risks are captured into the process and can be effectively managed
A risk management plan should be reviewed at least annually. The best way to make sure this occurs is to combine the review with annual business planning.
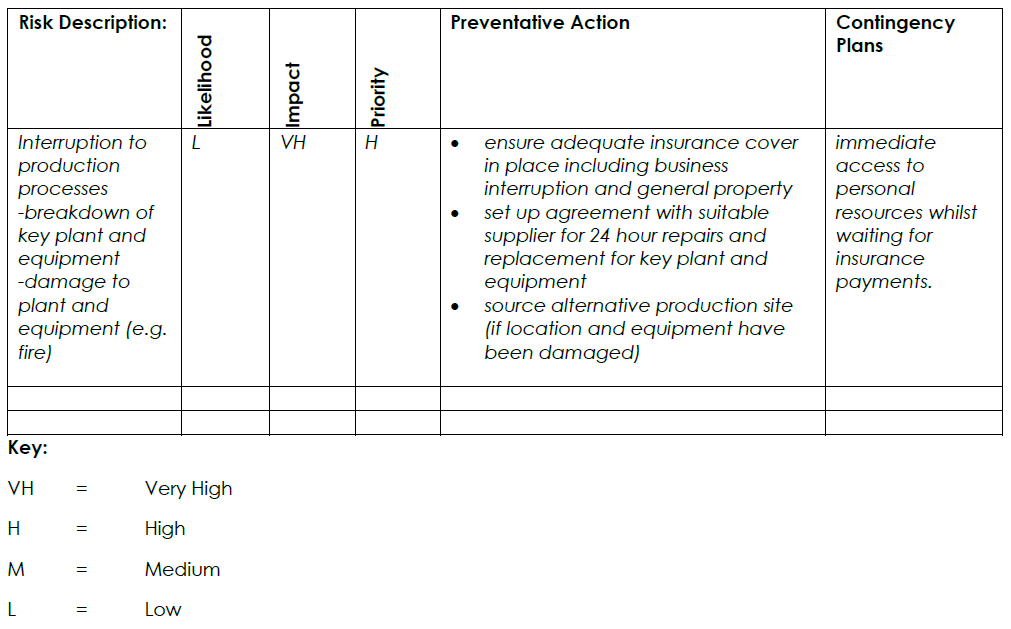
The risk management plan
The risk management plan is a document which outlines the risks faced by the business and provides guidance on risk mitigation strategies.
The risk management plan should contain:
identified risks
rating of the impact of the risk for the business (i.e. low, medium, high)
rating of the likelihood of the risk occurring (i.e. low, medium, high)
actions taken or to be taken to mitigate the risks
timeframes for review.
Risk management in a business should not be a stand-alone plan. There are relationships between risk management and many of the management processes and techniques that may be employed to ensure the successful operation of a business.
Good practice is to ensure that all of the following business areas are considered when developing the risk management plan:
business planning
occupational health and safety
human resources management
compliance
financial management
client management
contract management
quality assurance.
The risk management plan should be reviewed regularly and updated as needed to ensure all risks in the business are being covered.
Example:
We will be exploring the main parts of the risk management process in more detail in the rest of this learner guide, whilst learning more about monitoring, assessing and managing risk.
IDENTIFY POTENTIAL RISKS AND ASSESS THE IMPACT THEREOF IN A UNIT
All organisations need to manage risks but the good news is that many of the risks that face organisations on a daily basis are those that are within their own control. Many organisations have adopted a structured approach to risk assessment45. Risk assessment does not necessarily require sophisticated tools. They can be conducted simply by asking some key questions. Even for those events that are outside your control, there are steps you can take to avoid, contain or reduce adverse impact on the organisation.
If you were to ask your management team about risk, would your management team know:
What factors affect the organisation’s ability to accomplish its mission or its objectives?
What provisions had been made to contain, reduce or control risk?
In which processes were these controls installed?
How the effectiveness of these provisions is being measured?
What recent changes have been made to these processes to improve their robustness in preventing the risk having a detrimental effect on the business?
If you were also to ask your management team about the provisions it has made to mitigate against risk would it be able to explain what provisions had been taken to safeguard the organisation from:
Attack by competitors, disgruntled employees, computer viruses
Losing customers, suppliers, employees, reputation
Decline in orders, revenue, profit, market share
Dissatisfying customers, shareholders, employees
Prosecution by regulators, customers, employees
Delayed delivery
Delayed receipt of product or payment
Hazards injurious to health of personnel and/or the environment
Accidents to personnel and equipment
Breakdown of equipment, plant, machinery, relationships
Disruption to business continuity by computer failure, loss of information, strikes, weather.
Certain techniques can identify potential risks and assist in their elimination, reduction or control if the provisions are built into process design.
A risk assessment is simply a careful examination of what, in your work, could cause harm to people, so that you can weigh up whether you have taken enough precautions or should do more to prevent harm. Workers and others have a right to be protected from harm caused by a failure to take reasonable control measures.
Accidents and ill health can ruin lives and affect your business too if output is lost, machinery is damaged, insurance costs increase or you have to go to court. You are legally required to assess the risks in your workplace so that you put in place a plan to control the risks.
Use the Risk Management Process
Risk Assessment consists in the hazards identification and the analysis and evaluation of risks associated with exposure to the identified hazard. In this phase a comparison of the identified and analysed risk against given risk criteria will be done.
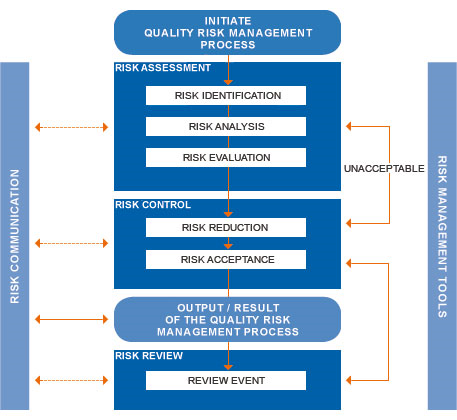
Risk Control includes risk mitigation which may include actions taken to reduce the severity and probability of harm for risks that fall into the “intolerable” category.
The implementation of risk mitigation measures can introduce new risks into the system or increase the significance of other existing risks. Hence, a revision of the risk assessment to identify and evaluate any possible change in risk after implementing a risk control measure will be done.
Every risk control measure will be verified for proper implementation as well as effectiveness in achieving the intended degree of risk mitigation, usually through an on-going validation process.
Risk Communication is the exchange or sharing of information about risk and its management between the decision makers and others. Parties can communicate at any stage of the risk management process. The included information might relate to the existence, nature, form, probability, severity, acceptability, treatment, detect ability or other aspects of risks to quality. This exchange need not be carried out for each and every risk acceptance.
The output of the quality risk management process should be documented when a formal process has been utilised.
Risk Review consists of the continuous improvement of the risk management results. The risk management approach will be introduced in the system and it might be used when new risks arise.
Example: Health and Safety Risks
If you work in a larger organisation, you could ask a health and safety adviser to help you. If you are not confident, get help from someone who is competent. In all cases, you should make sure that you involve your staff or their representatives in the process. They will have useful information about how the work is done that will make your assessment of the risk more thorough and effective. But remember, you are responsible for seeing that the assessment is carried out properly.
When thinking about your risk assessment, remember:
a hazard is anything that may cause harm, such as chemicals, electricity, working from ladders, an open drawer, etc. and
the risk is the chance, high or low, that somebody could be harmed by these and other hazards, together with an indication of how serious the harm could be.
Risk assessment is probably the most important step in the risk management process, but may also be the most difficult to accomplish and the most prone to error.
Uncertainty in the measurement of risk is due to the fact that no single metric embodies all of the information in the measurement. Normally, two quantities are being measured, e.g. extent of loss and probability of loss. A risk with a large potential loss and a low probability of occurring will be treated differently from one with a low potential loss but a high likelihood of occurring. In theory, both are of nearly equal priority, but in practice it can be very difficult to manage when faced with the scarcity of resources, especially time, in which to conduct the risk management process.
Means of measuring and assessing risk vary widely across different professions, e.g. a doctor manages medical risk and a civil engineer manages risk of structural failure.
If risks are improperly assessed and prioritised, time can be wasted in dealing with risk of losses that are not likely to occur. Spending too much time assessing and managing unlikely risks can divert resources that could be used more profitably.
Unlikely events do occur, but if the risk is unlikely enough to occur, it may be better to simply retain the risk, and deal with the result if the loss does in fact occur.
The fundamental difficulty in risk assessment is determining the rate of occurrence since statistical information is not available on all kinds of past incidents. Furthermore, evaluating the severity of the consequences (impact) is often quite difficult for immaterial/ intangible assets.
Asset valuation is another question that needs to be addressed. Thus, best educated opinions and available statistics are the primary sources of information.
Nevertheless, risk assessment should produce information for the management of the organisation in such a way that the primary risks are easy to understand so that the risk management decisions may be prioritised.
Identify Potential Risk Factors for Critical Processes
Risk identification sets out to identify an organisation’s exposure to uncertainty. This requires an intimate knowledge of the organisation, the market in which it operates, the legal, social, political and cultural environment in which it exists, as well as the development of a sound understanding of its strategic and operational objectives, including factors critical to its success and the threats and opportunities related to the achievement of these objectives.
Risk identification should be approached in a methodical way to ensure that all significant activities within the organisation have been identified and all the risks flowing from these activities defined. All associated volatility related to these activities should be identified and categorised.
Business activities and decisions can be classified in a range of ways, examples of which include:
Strategic – These concern the long-term strategic objectives of the organisation. They can be affected by such areas as capital availability, sovereign and political risks, legal and regulatory changes, reputation and changes in the physical environment.
Operational – These concern the day-today issues that the organisation is confronted with as it strives to deliver its strategic objectives.
Financial – These concern the effective management and control of the finances of the organisation and the effects of external factors such as availability of credit, foreign exchange rates, interest rate movement and other market exposures.
Knowledge management – These concern the effective management and control of the knowledge resources, the production, protection and communication thereof. External factors might include the unauthorised use or abuse of intellectual property, area power failures, and competitive technology. Internal factors might be system malfunction or loss of key staff.
Compliance – These concern such issues as health & safety, environmental, trade descriptions, consumer protection, data protection, employment practices and regulatory issues.
Whilst risk identification can be carried out by outside consultants, an in-house approach with well-communicated, consistent and co-ordinated processes and tools is likely to be more effective. In-house ‘ownership’ of the risk management process is essential.
The identification of the hazards in all aspects of work should be approached by:
walking around the workplace and looking at what could cause harm
consulting workers and/or their representatives about any problems they have encountered. Often the quickest and surest way to identify the details of what really happens is to ask the workers involved in the activity being assessed. They will know what process steps they follow, whether there are any short cuts, or ways of getting over a difficult task, and what precautionary actions they take
examining systematically all aspects of the work, that is:
temporary and part-time workers.
looking at what actually happens in the workplace or during the work activity (actual practice may differ from the policies and procedures manual)
thinking about non-routine and intermittent operations (e.g. maintenance operations, changes in production cycles)
taking account of unplanned but foreseeable events such as interruptions to the work activity
considering long-term hazards to health, such as high levels of noise or exposure to harmful substances, as well as more complex or less obvious risks such as psychosocial or work organisational risk factors
looking at company accident and ill-health records
seeking information from other sources such as:
manufacturers’ and suppliers’ instruction manuals or data sheets
occupational safety and health websites
national bodies, trade associations or trade unions
legal regulations and technical standards.
The identification of all those who might be exposed to the hazards:
For each hazard it is important to be clear about who could be harmed; it will help in identifying the best way of managing the risk.
Account should be taken of workers interacting with the hazards whether directly or indirectly, e.g. a worker painting a surface is directly exposed to solvents, while others workers in the vicinity, engaged in other activities, are inadvertently and indirectly exposed.
This doesn’t mean listing everyone by name, but identifying groups of people such as ‘people working in the storeroom’ or ‘passers-by’. Cleaners, contractors and members of the public may also be at risk.
Particular attention should be paid to:
gender issues and to,
groups of workers who may be at increased risk or have particular requirements:
workers with disabilities
young and old workers
pregnant women and nursing mothers
untrained or inexperienced staff
It is important to identify how these people might be harmed, i.e. what type of injury or ill health may occur.
Risk Description
The objective of risk description is to display the identified risks in a structured format, for example, by using a table. The risk description table overleaf can be used to facilitate the description and assessment of risks. The use of a well-designed structure is necessary to ensure a comprehensive risk identification, description and assessment process.46
By considering the consequence and probability of each of the risks set out in the table below, it should be possible to prioritise the key risks that need to be analysed in more detail.
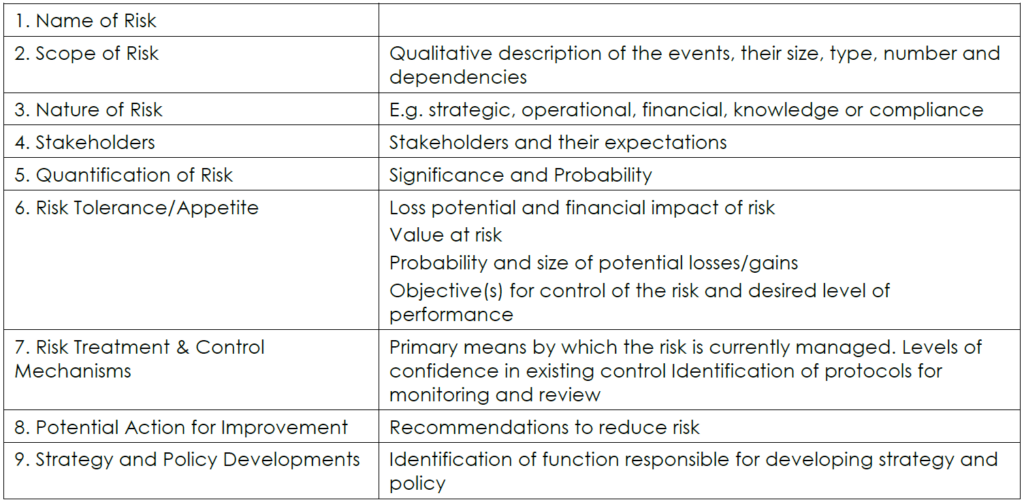
Identification of the risks associated with business activities and decision making may be categorised as strategic, project/tactical, operational. It is important to incorporate risk management at the conceptual stage of projects as well as throughout the life of a specific project / unit.
Methods and Techniques for Conducting Risk Assessment
There are various risk identification techniques that could be used, such as:
Brainstorming
Questionnaires
Business studies which look at each business process and describe both the internal processes and external factors which can influence those processes
Industry benchmarking
Scenario analysis
Risk assessment workshops
Incident investigation
Auditing and inspection
HAZOP (Hazard & Operability Studies)

There are various risk analysis methods and techniques that can be used, such as:
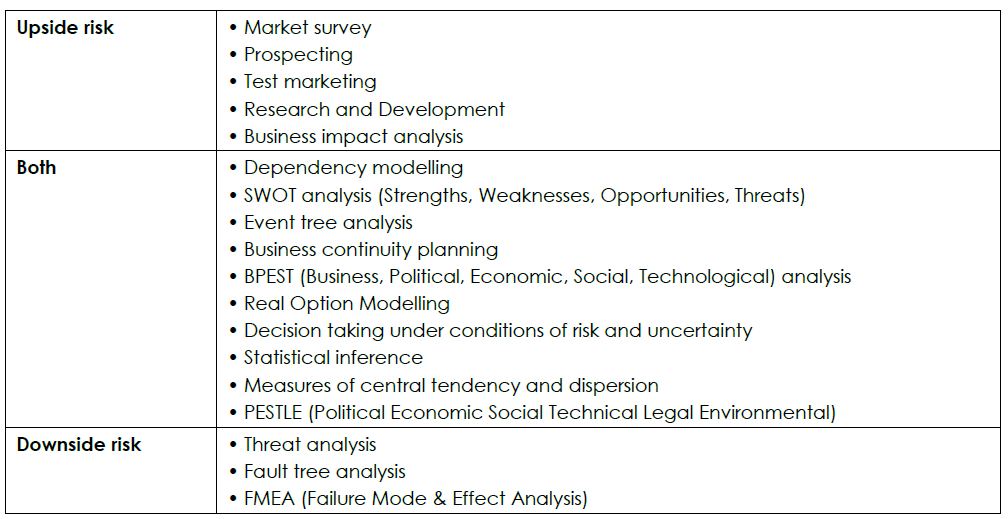
The risk assessment techniques can broadly be categorised into 4 areas:
Issue-based risk assessment – Looks at technical, commercial and managerial aspects and how their risks may impact on the plan. This could include a simple checklist to complete.
Checklist risk assessment – Checklists, whilst simple, in general suffer from drawbacks.
Qualitative risk assessment – Different systems exist like scoring and ranking or the use of high / low / medium assessments of impacts. Scoring requires a degree of subjectivity. As the name suggests, points are awarded according to the perceived degree of risk involved. The points are then totalled and an overall assessment of the risk established.
Quantitative risk assessment – We have already seen many techniques for assessing the impact of two activities with a range of values.
Issue-based Risk Assessment
Issue-based risk assessment has an advantage of being straight forward and generates potential problems largely based upon experience.
Being a method that is based upon previous experience there is a danger that old ground is covered and the obvious areas are investigated:
Opportunities for more creative thinking may be limited.
It is easy to compartmentalise your thinking in the relevant areas of commercial, technical etc and miss the relationships between the departments.
Whilst useful in some circumstances as they are simple you will need to be aware of their limitations.
Good review procedures from previous procedures will provide lessons that may well apply to other projects. You should be aware of these.
This method does not promote creativity and can encourage a narrow approach. Hence, many risks may well be missed.
This risk management method does not allow you to assess the impact of risks in a meaningful way that can be aggregated over the project or at interim points.
The aim is to cover the areas like financial, regulatory, etc. over the project lifecycle.
You would brainstorm each area to try and add some degree of creativity.
This method may just lead to a check list of ‘issues’ without much understanding of them in terms managing your unit’s risks, response and impact on the project / unit.
Checklists Risk Assessment
The checklist is a general result of the ‘issue’-based method of assessment and the typical items to be aware of are:
Can end up concentrating on historical experience perhaps at the experience of new or future risks.
Can be considered as exhaustive with the danger of becoming complacent.
Does not easily assess the total project risk.
In addition:
Interdependence of schedule activities are hard to visualise
Risks identified are not readily prioritised
If it’s not on the list it is likely to be ignored
The list may be orientated to a particular project and miss the experiences of others
Necessary detail may be lacking
Can promote a simple view of risks and the risk management process.
Any checklist used should be considered as an initial help to a more formal project / operational management procedure:
You should be trying to generate a list that is not so long that it becomes difficult to manage or starts to include trivial risks.
As well as looking at the internal risk of activities you should also consider potential external problems.
These sort of check lists tend to generate perceived risks based upon historical events. This is a good thing as you don’t want to repeat yesterday’s mistakes.
However, be aware of trying to encourage the ‘brainstorm’ used to generate the list to consider new and future events.
One problem with a list is that the project management team can see it as exhaustive. Beware of complacency.
This method is not very good at trying to assess the overall impact of risk on the total project / operational management plan.
Qualitative Methods of Risk Assessment
Qualitative methods try to compare ranges in a simple fashion. Specific values are not given to the impacts.
Methods include a simple scoring system and the use of low / medium / high.
Even so, qualitative methods have numerous advantages over the issue based method but there are a few pitfalls in the interpretation of the data.
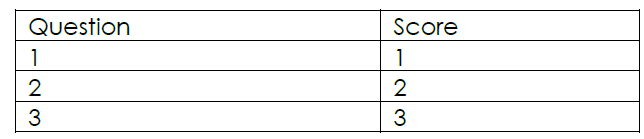
Risk analysis is based upon some form of set question system that tries to attribute a particular value to the impact if the risk materialises. Very simplistically it could be:
- Set up a series of questions. If the answer is yes score as shown, if no score zero.
2. Alternatively, a series of questions could be set that require a degree of interpretation and subjectivity to choose a score within a possible range.
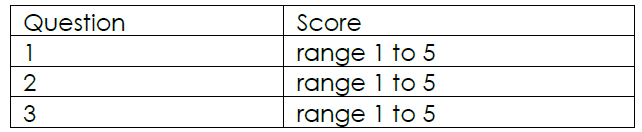
- The choice of 1 might be low risk and 5 high risk. Naturally, the questions that you attribute to the project management task could be quite detailed in their description of the level of risk.
- Eventually, for a given task, the total score is calculated. For example, if the total score is 23 it could be interpreted as:
In this case the risk could be considered to be medium. What medium means in practice would require some agreement within the management team.
The major problem with the ‘score’ based system is that it depends on the individual’s interpretation of the scoring system. It can be too subjective.
In addition, there may be some confusion with the likelihood of the risk occurring and its impact on the project. The risk management system could show a high impact but have virtually no chance of occurring and may therefore not be a problem. You must be aware of this when using these methods.
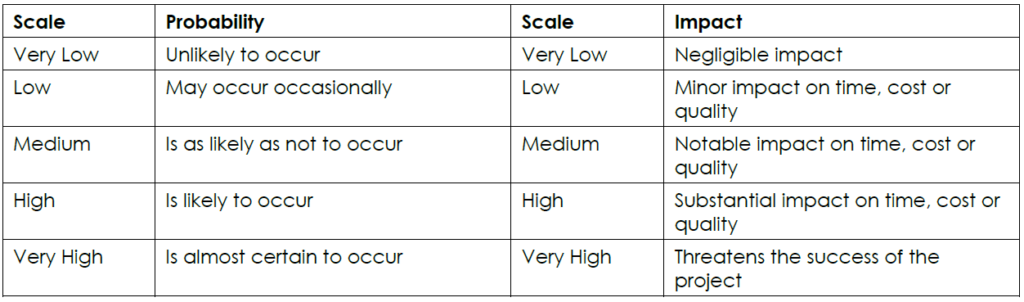
Use enough categories so that you can be specific but not so many that you waste time arguing about details that won’t actually affect your actions. Experience suggests that a five-point scale works well for most projects. A suggested scale is:
Example:
The total risk of the project can be confused with the total score achieved by adding up the individual scores. This is a very simplistic view and is another drawback of this approach.
The risk of individual project management tasks is not additive. Many tasks depend upon others in the schedule.
So, whilst the simple nature of this method may have its uses there are still disadvantages.
In summary:
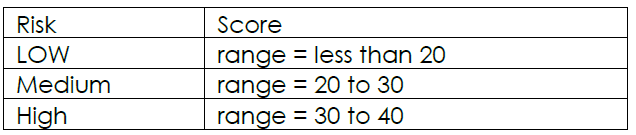
These methods try simply to determine the size of the effect based upon threshold:
o less than a particular value (safe)
o in between (medium risk)
o higher than a particular value (high risk)
Can be seen as meaningless or subjective
Can confuse likelihood with impact and obscure priorities – may miss new high risk activities
Quantitative Methods of Risk Assessment
This approach is based upon the project / operational management plan (schedule) which has been put together by considering not only all of the individual tasks, but including their relationships.
The qualitative definition of risk is one with which most managers will be both familiar and comfortable. However, at the risk of introducing a degree of circularity into the reasoning, none of this means anything at all in real terms unless you have set some kind of thresholds for your qualitative definitions.
What do we mean by a medium risk? If a risk is likely to cause a five-week delay to your project or cost you R10k where does that sit on the scale of ‘very low’ to ‘very high’ in relation to your particular project? You must do these threshold definitions and understand what are high cost and time implications for your project before you can assess risks in a meaningful way. The following table suggests a general measure of impact in the education environment.
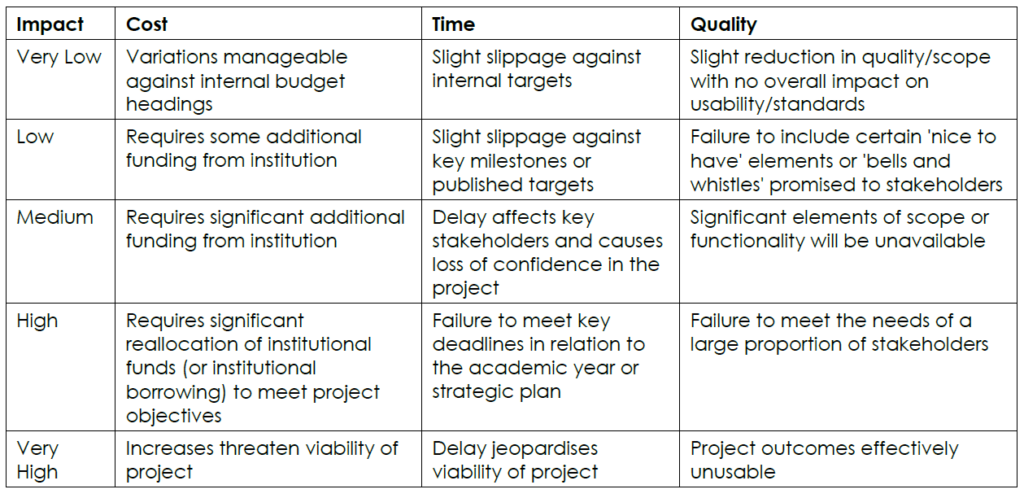
There are many variations on this table. In the commercial world percentage scales are often used for the cost and time components. The scale frequently goes from less than 5% variation (low) to greater than 20% variation (very high).
The risk management process will begin with the summary initial plan and develop the ‘reference’ and base plan (agreed, accepted initial plan for implementation).
It uses data that already exists in assessing the risk of not completing a task and the potential costs.
The units of risk measurement will be the same as for the durations and cost measurements.
This makes it much easier for individuals to gauge the risk and to come to informed decisions.
In summary:
Based upon plans already in use
Uses cost and schedule breakdown information
Measures risk in the same units as task durations and costs
Easily informs decision making for milestone dates and budgets.
Adapted from: www.risk-management-basics.com
Please see Appendix A for notes about how to map information gathered.
Risk Assessment Tools
We will explore a few of the Risk Assessment tools below, namely:
What-if analysis
Checklist of known hazards
Hazard and operability study (HAZOP)
Failure mode and effect analysis (FMEA)
Fault Tree Analysis (FTA)
Ishikawa
Preliminary Hazard Analysis (PHA)
What-if Analysis
Use a what-if analysis to identify specific hazards and hazardous situations. What-if questions are asked about what could go wrong and hazardous consequences are identified and analysed. This type of analysis is a brainstorming activity and is carried out by people who have knowledge about the areas, operations, and processes that may be exposed to hazardous events and conditions.
Checklist of Known Hazards
Use a checklist of known hazards to identify your hazards and hazardous situations. The value of this type of analysis depends upon the quality of the checklist and the experience of the user.
Use a combination of checklists and what-if analysis to identify your hazards and hazardous situations. Checklists are used to ensure that all relevant what-if questions are asked and discussed, and to encourage a creative approach to risk assessment.
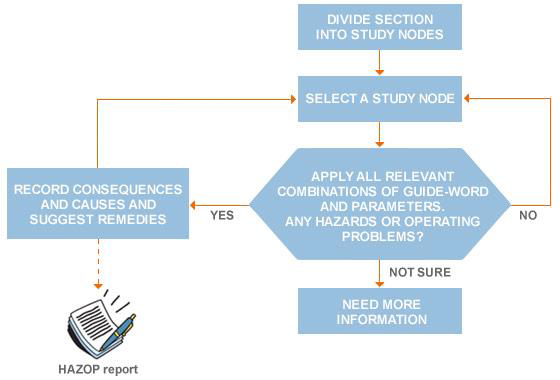
HAZOP
Use a hazard and operability study (HAZOP) to identify your hazards and hazardous situations. If you need to do a very thorough analysis, this method is for you. However, it requires strong leadership and is costly and time consuming. It also assumes that you have a very knowledgeable interdisciplinary team available to you, one with detailed knowledge about the areas, operations, and processes that may be exposed to hazardous events and conditions.
Hazard and Operability (HAZOP) analysis is a technique that allows you to identify and evaluate, caused by deviations from the design or operating intentions problems that may represent risks to personnel or equipment. These deviations are recognised by using so-called “guide-words” applied to process parameters.
The main “guide-words” are listed in the following table.
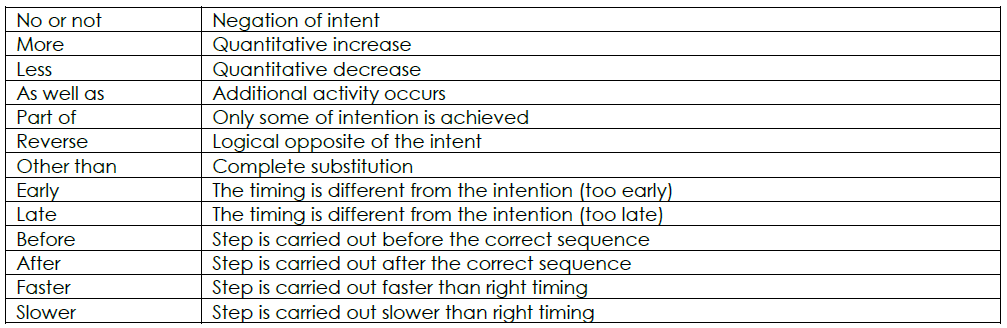
HAZOP technique was originally developed to study plants and process systems. It also often applied to operators, software and procedures.
HAZOP is realised by using a work-sheet that generally includes the following columns:

ID number
Guide-word
Type of deviation
Potential causes
Consequences
Safeguards/controls
Actions required/recommendations
Responsibility
In order to apply HAZOP technique, process flow and layout diagrams, data sheets and operating instructions should be available.
A HAZOP study is very often used as a systematic technique for identifying hazards or operability problems throughout an entire facility. One (usually a team of people) examines each segment of a process and lists all possible deviations from normal operating conditions and how these might occur.
What deviations could arise?
How can these arise?
What are the implications?
Any surrounding implications?
Example:
A pipe could break, if the supports are not adequate.
Gas will escape from the break.
A massive explosion will ensue.
Damage to plant and surrounding property, risk to life and limb.
A node is a specific location in the process in which the deviations of the design/process are evaluated.
The first step is to collect documents and drawings as mentioned before. After that it is possible to divide the facility into different nodes and for each one evaluate deviations, all potential causes and related consequences, also listing controls and recommendations.
HAZOP studies are very often used in practice and in America it is estimated that half of the chemical industry used the HAZOP technique for all new facilities. The normal time between reviews of existing facilities is 1½ – 5 years and the use of the technique is increasing.
FMEA
Use a failure mode and effect analysis (FMEA) to identify potential failures and to figure out what effect failures would have. This method begins by selecting a system for analysis and then looks at each element within the system. It then tries to predict what would happen to the system as a whole when each element fails. This method is often used to predict hardware failures and is best suited for this purpose.
Key concepts which characterise FMEA and define the risk are:
Function (or process step) – the task that the system, design, process, or service must perform
Failure – functional defectiveness that does not meet the customers’ requirements. It is the inability of the system to perform based on the design intent
Failure mode – the physical description of the manner in which a failure occurs
Cause of failure – the root cause of the listed failure
Effect of failure – the outcome of the failure of the function from a local or global point of view.
Current controls – implemented controls to prevent causes of the failure from occurring
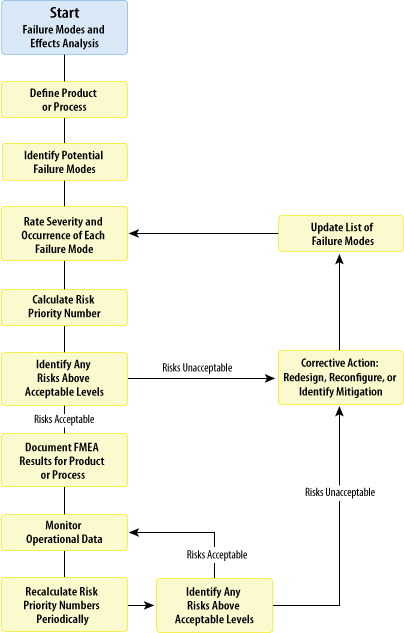
In order to categorise and prioritise risk level three parameters need to be defined:
Severity – it indicates the seriousness of the effect (consequences) of the failure mode
Occurrence – it represents the estimate number of failure that could occur for a given cause
Detection – it corresponds to the likelihood that the proposed control will detect a specific cause of a failure
Risk priority to identify a corrective action implementation order is calculated through combination of these three parameters after defining a threshold of risk acceptability.
FMEA/FMECA is frequently used in combination with other techniques to reach multiple benefits, e.g. in order to identify causes of failure a specific Fault Tree Analysis (FTA) can be developed.
Use a fault tree analysis (FTA) to identify all the things that could potentially cause a hazardous event. It starts with a particular type of hazardous event and then tries to identify every possible cause.
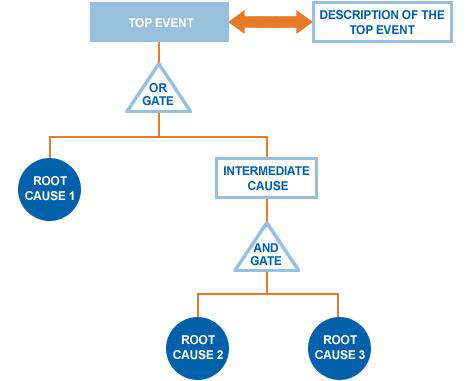
Main steps for build FTA following:
- System definition: the definition of the system is essential to understand the environment and the process involved in the system itself and can be obtained using a mapping technique.
- Top event identification: the top event must be clearly and unambiguously identified together with the definition of the boundaries that edge the analysis.
- Tree development: the tree is developed by the definition of the events and conditions that can generate the defined top event, the connection of these events by logic gates, proceeding until the appropriate level (i.e. the level where root events are independents or where no data exist for that event).
- Fault tree evaluation: the evaluation of a fault tree is based on the identification and classification of minimal cut sets, i.e. the minimal set of root events whose simultaneous occurrence ensures that the top event occurs.
- Top event probability estimate: the estimation is based on statistical calculations that combine the probability of failure of the different basic events.
ISHIKAWA
This technique was developed in 1969 by Kaoru Ishikawa, who pioneered quality management processes in the Kawasaki shipyards, and in the process became one of the founding fathers of modern management.
The Ishikawa diagram, also called “Fishbone” or “Cause-and-Effect diagram”, is a graphic tool used to identify potential causes (i.e. sources of variation in a process) for an effect or a problem.
It is most effective if made by a team (brainstorming) rather than by individuals and is used for product design and quality defect prevention.
The potential causes identified by the team are usually grouped into categories that identify sources of variation. Generally these categories could be the 6 M’s:
MAN: personnel involved in process
MOTHER NATURE: environmental conditions
METHODS: procedures, instructions, etc.
MACHINES: equipment
MEASUREMENTS: data generated from the process
MATERIALS: anything used in the process
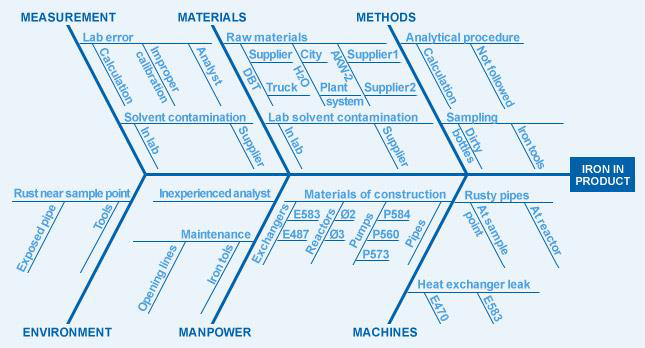
The problem of interest is inserted on the right of the diagram at the end of the main “bone”. The identified categories related to the problem are drawn as bones off the main backbone. Brainstorming is typically done to add possible causes to the main “bones” and so on. This subdivision into ever increasing specificity continues as long as the problem areas can be further subdivided. The practical maximum depth of this tree is usually five levels.
PHA
Preliminary Hazard Analysis (PHA) is based on exploiting prior experience or knowledge of a hazard or failure to identify future hazards, hazardous situations and events that can cause harm and estimate their probability of occurrence for a given activity, facility, product or system.
The objective of the PHA is to identify as early as possible the main hazards and accidents that may arise during the life of the product.
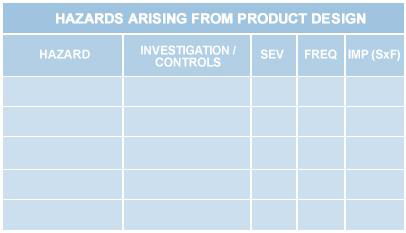
After hazard identification and quantification in terms of severity and frequency of the event / consequence, it is necessary to associate a possible remedial measures to reduce risk in an acceptable area.
This technique can be used as initial risk assessment either when the analysed system is not yet clearly defined or when exhaustive information is not available. It can be useful when analysing existing systems or prioritising hazards where circumstances prevent a more extensive technique from being used.
Hazard identification can be made through:
- Evaluation of similar systems
- Review of other hazard analyses (for similar systems)
- High level risk assessment
PHA should be performed as early in the project life cycle as possible in order to gain maximum benefit by understanding hazards. In fact, any change is less expensive and easier to implement in the first stages of design, thus reducing the number of problems.
Adapted from: www.ptm-consulting.it
Use of Data: Risk inspections, questionnaires and incident report forms
Most firms do not have enough accidents to justify sophisticated statistical analysis. Even in large concerns, conditions may vary between operating divisions and localities.
However, the information on accidents and other incidents (near-misses) provided by accident report forms can be used to:
- measure the performance of line managers and supervisors
- determine which operations need correction
- identify hazards
- motivate workers and managers toward loss control
Examples
Suppose that a disproportionate number of accidents occur during the night-shift. Perhaps:
The foreman or supervisor is a little slack
Some employees have taken on additional ‘day’ jobs and are tired when they come on shift
Lighting is faulty – insufficient or flickering lights, heavy shadows
Night-time temperatures are too low for comfort. The opposite might happen during the day, when it is too hot
If one employee’s name keeps cropping up, perhaps he
Has personal problems, affecting his work
Is being overworked
Needs better training
Should be moved to some other line of work, before he injures himself
Accidents at a particular machine might show a need for improved safety devices, better operating procedures, or even replacing it with a new and safer model.
Other Sources of Information
The experience of other firms may suggest other risks resulting in losses to them, which may be “accidents waiting to happen” as far as the present company is concerned.
The American risk management guides suggest a list something like this:
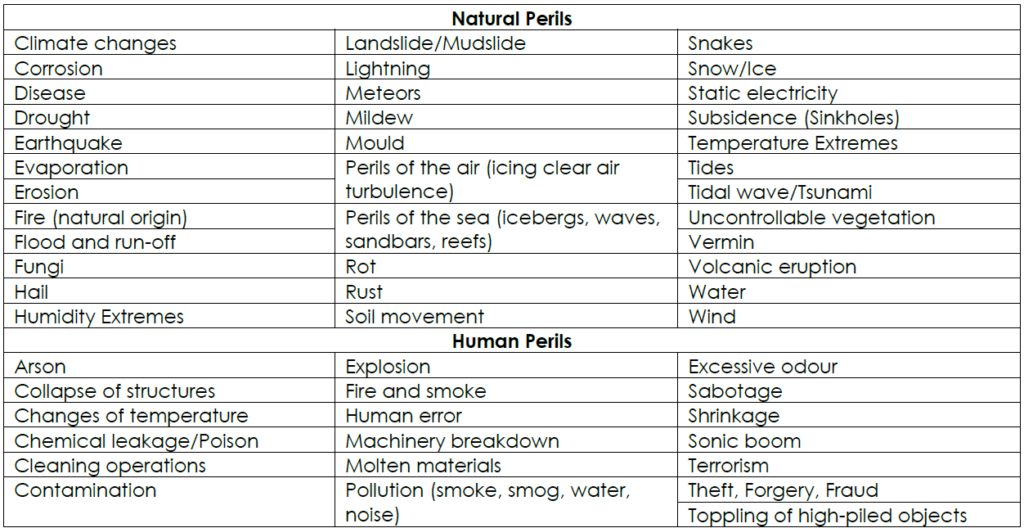
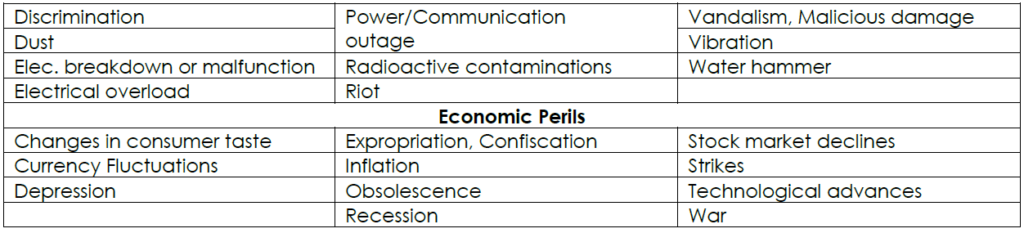
This classification may be of considerable value in implementing risk control measures since it includes several of the gradually operating causes excluded by most insurance policies. It is meant as a reminder, not a hard-and-fast set of definitions.
New hazards also come to light through experimentation under controlled conditions.
Identify Possible Scenarios that could Constitute a Risk
Scenario modelling (of interactions between hazards, vulnerabilities and exposures) is a crucial step which informs sound risk ranking and planning considerations.
Results from recent analyses and performance reviews recognise that “comprehensive planning, including using the results of disaster simulations, can help organisations better prepare for potential disasters and thereby mitigate their effects”. (Ref: GAO-07-114 SBA Disaster Preparedness, Feb 2007, p. 3-4)
Generate and model scenarios by identifying what, why, where, when and how events could affect the entity (business).
Premise predicaments – and tease out issues for prevention, preparedness, response and recovery.
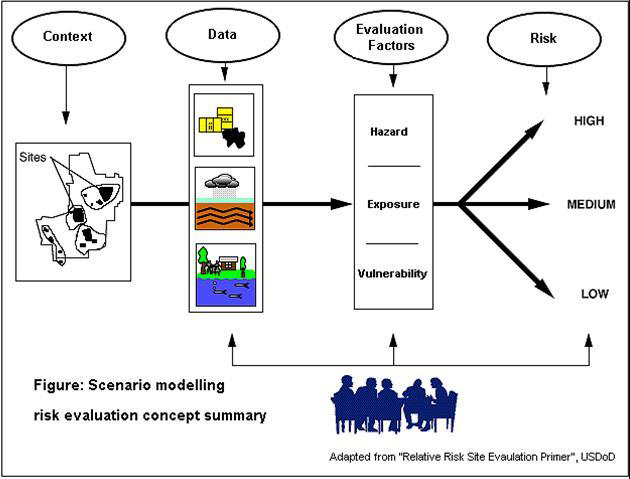
Scenarios provide an excellent platform to engage stakeholders, assess risks and exercise key management competencies.
Use quality planning processes (such as those outlined in the table below) to ensure tailored outcomes are achieved.
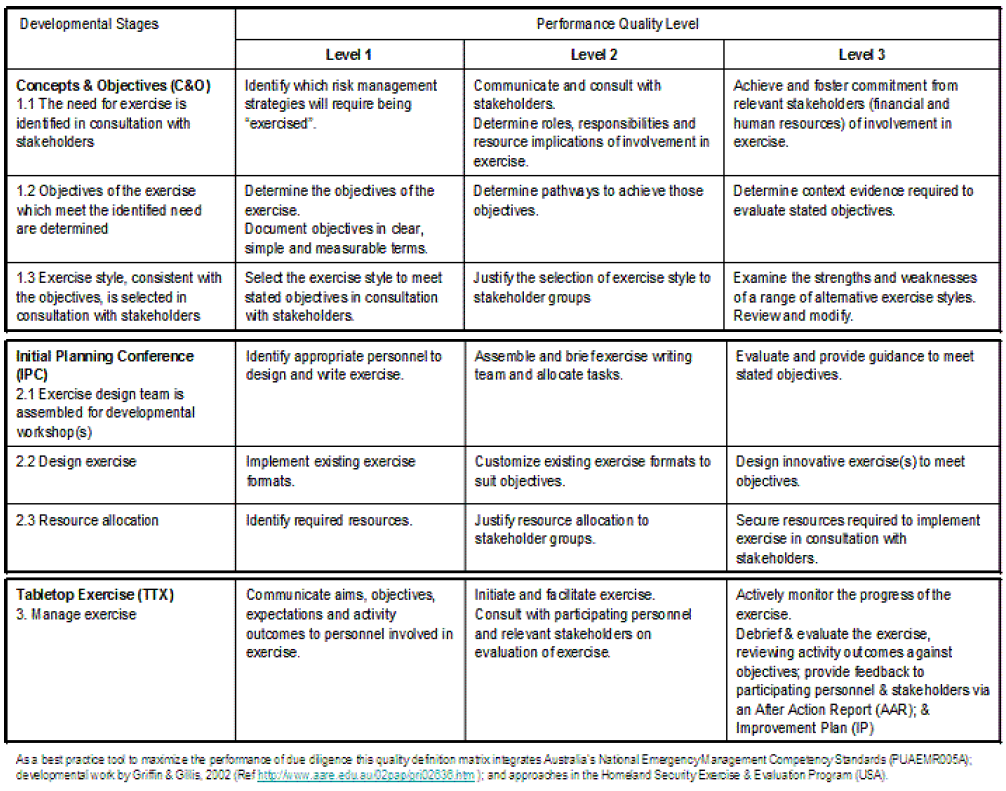
Risk inspections, questionnaires and incident report forms should have revealed a number of potential hazards or risks.
Please see Appendix B for an example risk assessment document that can be used in the office environment.
We cannot deal with all of these in detail, but the following are some basic considerations:
Organisational records as a risk
Records can be classified in one of the three following categories:
Vital records
Important records
Useful records.
Vital records are irreplaceable. Important records can be obtained or reproduced at considerable expense and only after considerable delay. Useful records would cause inconvenience if lost, but can be replaced without considerable expense.
Vital and important records should be duplicated and stored in an area protected from fire or its effects.
Records kept in the computer room should be minimised and should be stored in closed metal files or cabinets.
Records stored outside the computer room should be in fire-resistant file cabinets with fire resistance of at least two hours.
Protection of records also depends on the particular threat that is present. An important consideration is the speed of onset and the amount of time available to act. This could range from gathering papers hastily and exiting quickly to an orderly securing of documents in a vault. Identifying records and information is most critical for ensuring the continuity of operations.
A systematic approach to records management is also an important part of the risk analysis process and business recovery planning.
Additional benefits include: reduced storage costs, expedited service, and government statutory compliance.
Records should not be retained only as proof of financial transactions, but also to verify compliance with legal and statutory requirements.
In addition, businesses must satisfy retention requirements as an organisation and employer. These records are used for independent examination and verification of sound business practices.
Government requirements for records retention must be analysed. Each organisation should have its legal counsel approve its own retention schedule. As well as retaining records, the organisation should be aware of the specific record salvage procedures to follow for different types of media after a disaster.
Fire as a risk
Fire is a rapid, self-sustaining energy conversion system, where energy stored in fuel is released as heat and, usually, visible light.
Means of Control
Fires can be avoided, controlled or put out by interfering with these requirements:
Heat: probably the easiest to remove. Cooling with water, preventing radiation (e.g. dry powder), slowing down combustion by venting hot gas. Better still, eliminate ignition sources.
Fuel: remove the fuel from the flame zone and the fire will go out. Examples: fire breaks; turning off supply of gas or liquid fuels, blanketing fuel with a vapour barrier (e.g. foam).
Oxygen: remove (very unusual), restrict, or dilute the oxygen in the flame zone to (generally) below 16% and the fire will be extinguished. Examples: dilution by inert gas such as Carbon Dioxide (CO2) or steam, closing down air intakes, limiting the openings in a building, breaking the air up into bubbles (high expansion foam), dropping a lid on the fuel or smothering with a blanket.
Note: Some fuels, e.g. explosives, contain their own oxygen supply in the form of oxygen rich compounds.
Chain reaction: Interfering with the chain reaction by means of chemicals can prevent it going to completion and thus prevent it releasing the stored heat of the fuel. Alternative products with high levels of stored energy are produced with the result that insufficient heat is released to sustain the fire. Examples: the action of BCF and dry powder.
Fire Detection and Extinguishers
Every commercial property should be fitted with:
first-aid fire-fighting equipment
smoke or heat detectors
an evacuation alarm
an automatic sprinkler system.
First-Aid Equipment
This includes hand-held extinguishers, and hose reels. Hand-held extinguishers have a limited capacity, but are useful on small fires in their early stages. They should be mounted in clearly marked, visible positions, as near as possible to exit points.
Hose reels have a better fire-fighting capacity, but cannot deliver a sufficient volume of water to contain a larger fire. They must not be misused for other purposes, and must not be obstructed in any way. The hose should be able to reach any part of the area being protected.
Smoke Detectors
In many kinds of fire, the early smouldering stages give off quantities of smoke. The early warning provide by a smoke detection system is especially valuable in hotels and other residential buildings, where occupants may otherwise be overcome by smoke inhalation in their sleep.
Heat Detectors
In fires where heat is rapidly evolved, perhaps without a great deal of smoke, heat detectors may give early warning. During South African summers, normal heat ranges, particularly at roof level, can be high, and the detection range must allow for this.
Evacuation Alarms
An early priority is getting personnel to a place of safety. There should be an established system of fire drills.
Automatic Sprinklers
An automatic sprinkler system consists of water pipes and heat operated valves (sprinkler heads). Fire is automatically detected, the alarm given, and water delivered to the seat of the fire. This is like having one fireman for every 10 square meters of floor area, 24 hours a day. The fire can be extinguished or at least kept under control until the fire brigade arrives.
Apart from installation and maintenance costs, some possible snags are:
Accidental discharge, by knocking one of the heads
Faulty stacking of goods, so as to restrict the flow of water from the head
Inadequate or fluctuating water supply. Sometimes several heads are activated. The water supply must provide the specified flow for a sufficient time. Additional storage tanks and booster pumps may be necessary
Deliberately or accidentally closing the main shut-off valve. Usually these are padlocked or strapped in the open position. The fire brigade, on attending the fire, can then decide when the sprinkler should be turned off.
In dealing with one risk, we must be careful not to create another. Water is not suitable for electrical fires, due to the risk of short circuit or electrocution, although it might be acceptable if the power has been turned off. Dry powder extinguishers can cause damage to delicate machinery (or involve many hours of labour in dismantling and cleaning). An accidental release of CO2 gas may asphyxiate a repair man. Automatic sprinkler systems can cause extensive damage to stocks of paper, although this might be preferable to a devastating fire.
Prevention and Control
Factors to think about:
The inception risk, how a building is occupied; and the processes or hazards associated with such occupation
The propagation risk, the extent to which the size and layout of the premises and the presence of combustible materials may facilitate the spread of fire
The concentration of values involved; that is, the extent to which high value materials which are subject to risk are concentrated within relatively small areas
The construction of the building; to assess the degree to which it can resist a fire, or arrest its progress
Susceptibility to damage. Foodstuffs are easily contaminated by smoke. Electronic components may be affected by smoke, or even by a relatively small increase in temperature.
Sources of Ignition
Most fires occur because activation heat energy is introduced into an otherwise harmless situation in which combustibles are sitting waiting in contact with the oxygen in the air. (About 21% of the air is oxygen).
Common ignition sources in general order of frequency are:
Electricity
Smoking
Arson
Overheated materials
Hot surfaces
Open flames
Cutting and welding
Friction
Spontaneous combustion
Exposure to other risks
Chemical reactions
Mechanical sparks
Static sparks
Molten substances
Lightning.
The question of which best to control – the fuel or the heat, is sometimes determined by the state (or phase) of the fuel. Liquid fuels and gaseous fuels are much more mobile and will tend to ‘seek out’ the energy source. They are therefore more difficult to contain than solid fuels.
Explosion and Detonation as a risk
An explosion is a sudden and violent release of large amounts of gas or water.
Detonation is an explosion in which the speed of reaction through the reacting material is equal to or exceeds the speed of sound. A shock wave is produced even if not contained.
Deflagration is an explosion in which the speed of reaction through the reacting material is less than the speed of sound. A shock wave is only produced if the deflagration occurs within a confined space. This may sound a bit technical, but it is important when considering surrounding property damage, or liabilities. Usually, detonation is more dangerous than deflagration.
Causes
Explosions may arise from:
Bursting of pressure vessels, such as gas cylinders and boilers
Very rapid heat reactions producing large volumes of gas and/or vapours.
It is not always realised that dust can cause an explosion. Dusts have a larger surface area than the solid materials from which they are formed, and when the dust is in the form of a cloud the individual particles are surrounded by air. As a consequence their rate of burning is much greater than that of bulk solids.
Provided that the particles are neither too far apart nor too close together, ignition will be followed by a spread of flame through the dust cloud as successive zones are heated to ignition temperature.
The spread of flame results in a build-up of pressure by the expanding hot gases creating pressure waves. These travel ahead of the flame. Any dust lying on surfaces in the path of the explosion will be thrown into the air, and can cause a secondary explosion more violent than the first.
Prevention and Control
It is possible to take steps to prevent and minimise loss caused by the explosion of:
Inflammable or explosive gases and vapours by:
o Providing mechanical exhaust fans to ventilate the area of any build-up of gases or vapours to a safe area outside the building;
o Flame proofing all electrical equipment;
o The elimination of all other possible ignition sources;
o The use of safe working practices and good housekeeping standards.
Dusts by:
o Enclosure of plant, processes and equipment to prevent dust escaping and reaching ignition sources;
o Dust extraction to a metal container outside the building so as to prevent the accumulation of explosive dust;
o Removal or protection of ignition sources including the flame proofing of electrical equipment;
o Working under an inert atmosphere or under liquid;
o The use of safe working practices and good housekeeping standards;
o Installing electromagnetic or metal detecting safety switches in the feed areas of grinders to detect all tramp iron, to prevent both spark and damage to the machinery;
o Prevention of the accumulation of dust. Layers of dust tend to have lower ignition temperatures than dust clouds. The differences can be very significant – over 200 degrees centigrade – in the case of many agricultural products and certain plastics. When dusts are allowed to accumulate on surfaces which are apparently at a safe temperature they can begin to smoulder. If the dust is then dispersed an explosion can occur. Ignition temperatures decrease as layers become thicker.
Protecting the plant by designs that withstand or isolate the explosions. Pressures of 700kPa can be generated. Most plant cannot withstand pressures much greater than 20kPa.
Relieving plant explosions by diverting the force of the blast harmlessly through vents, ducts or bursting panels.
Suppressing plant explosions by using the pressure from an explosion in its early stages to release a chemical which suppresses the explosion.
Remember that the actual explosion could occur at other premises. At a sweet factory, the entire day’s production was ruined when a nearby explosion shattered a glass skylight.
Other Controls
Other control measures include:
Free run-off of surface water, even under extreme conditions;
Securing any loose roofing material or wall cladding;
Hail nets or other shelter for vehicles;
Check that downpipes box gutters and drains are in good condition and free from blockages;
Check water supply pipes and other plumbing ;
Avoid flat or low-pitched roofs. Hail or even snow can accumulate and cause a collapse;
Watch out for construction work in the area, which can alter the normal water flows.
Storm, Flood, Water Damage as a risk
Pallets
The standard control measure is to palletise – raise items at risk a few centimetres off the floor. (Not much help when water comes from above). If real flooding occurs, water and debris sweep through the premises, leaving a residue of mud and rubbish 30 cm, or more, deep. This might be further contaminated by picking up oils and chemicals released from damaged containers.
Other control measures include:
free run-off of surface water, even under extreme conditions;
securing any loose roofing material or wall cladding;
hail nets or other shelter for vehicles;
check that downpipes box gutters and drains are in good condition and free from blockages;
check water supply pipes and other plumbing ;
avoid flat or low-pitched roofs. Hail or even snow can accumulate and cause a collapse;
watch out for construction work in the area, which can alter the normal water flows.
Theft as a risk
Situation
Some aspects of risk control can only be implemented prior to building, and the following should be taken into account:
The type of neighbourhood;
The level of lighting around the area at night;
The level of activity in the area during both daylight and night-time.
Construction
Most of the possible means of reducing the risk must be incorporated at the time of building, though some remedial work can be undertaken at a later date, such as providing additional protection for access points. Consideration should be given to such questions as:
The materials used in the building. Do they offer resistance to the would-be thief?
The layout of the building and any possible areas of concealment, such as
o Yards and enclosed areas. Can the lighting be improved?
o Boundary walls and fences. Can glass or razor wire be placed at the top of them to act as an
additional deterrent? An electric fence may be an option.
Access points both internal and external :
o Doors and windows. Are they heavy duty or substandard? Are window bars strong?
o Sewage and drainpipes. Is a spiked umbrella fixed at a suitable height on each of them or are they rebated into the brickwork?
Occupation
Occupation is perhaps the most important aspect as it determines to a large extent the attractiveness of the premises to the criminal because of the goods likely to be stored on the premises. It is difficult to see how the risks associated with a particular occupation may be eliminated as they are a fundamental part of that occupation. However, the risks involved can and should be minimised and consideration should be given to:
The type of goods stored and used in the premises. Are they easily transported and disposed? Can they be identified?
Is there ever a large accumulation of cash on the premises? Can this be avoided?
How are the goods and cash stored?
Other Precautions
There are other precautions. Paying attention to the little things can often bring considerable benefits as far as deterring the would-be thief from entering the premises. Precautions may be taken, such as:
Ensuring that the site is able to be securely fenced; Ensuring that all aspects of the exterior of the building are well lit at night, particularly doors and windows, planting trees or shrubs that will provide concealment to the criminal should be avoided;
Not leaving ladders, wooden pallets or similar items lying around outside the building as these can be used to gain access to the roof. In addition to providing access, these articles as well as any waste and unused packing material, are often used to start fires which can cause major damage to the building;
Making sure that all of the doors and windows to the premises are securely locked so that the thief has to use more time in trying to get into and out of the premises. Don’t hide an entrance key outside the premises, and ensure that all exit doors require a key to open them;
Not leaving attractive goods in full view;
Not leaving attractive goods in unsecured areas inside premises during non-working hours;
Installing security lighting to highlight intruders both inside and outside the premises;
Immobilising fork hoists, gantry cranes and any vehicles left inside the premises overnight;
Not storing money in the till overnight. Always empty tills and leave them open at night.
Machinery as a risk
Risk Control
To a large extent, this depends on proper maintenance and operating procedures, combined with protection against the obvious physical risks.
From an interruption standpoint, the questions include:
Is this the only machine of its kind at the premises, or are there back-ups, even perhaps at other companies in the group?
Is it working to full capacity, or could extra shifts be worked to make up for interruption time?
Are spares readily available? What stock of spares should be kept on the premises?
Arrangements with the machine suppliers or agents for rapid repair service?
Would it be worthwhile to buy a stand-by machine, or could the work be sub-contracted?
Computers as a risk
The risks arising out of the ownership and use of computers have become very significant in recent years, as has the dependency of organisations on them, and as the value of information to the operation of the organisation has been recognised.
The risk reduction measures that should be taken therefore need to ensure that:
The computing facility is available when required by the organisation;
Misuse of computer time is minimised;
The information is not:
o corrupted
o stolen or removed
o destroyed either deliberately or accidentally
Possible measures would include:
Careful selection of staff;
Strict implementation of standards for :
o operating programming
o systems design;
o division of duties e.g. programmers not allowed to operate;
o restricted and controlled access to the computer and its files;
o integration of the clerical and computer systems;
o control over the development and implementation of new systems and changes to existing systems in terms of both cost and time;
o regular financial audits.
Fidelity as a risk
Risk Control
This is closely related to Computer Control, except that opportunities for dishonesty are opened to a wider range of employees.
Control measures include:
Careful selection of staff. Sometimes, careful enquiries reveal a past history of dishonesty;
Implementing and enforcing strict procedures for handling stock and money;
Two or more signatures to cheques or money transfers;
Regular financial audits;
Good staff relations.
Liability as a risk
Risk Control
A liability claim is the consequence of an event, not the event itself. Legal liability risk control programmes overlap with other areas of risk control, except that they concern danger to other persons and their property, arising out of our operations and actions. This might be a positive act, or an omission. Could a reasonable man have foreseen the harm, and could he reasonably be expected to prevent it?
Important aspects are:
Liability for defective products
Liability for death or injury, or damage to property
Pollution, seepage and impairment of the environment
The risk manager should concern himself with the products marketed, the uses to which these are put, and the contract conditions under which they are supplied.
Personnel Risks
Hazards
As already pointed out, most preventable accidents are of human origin. People fall into the habit of doing things that really do not make sense, such as:
Standing on a wobbly ladder to adjust a drive belt, or reach something on a shelf;
Working on revolving machinery while wearing loose flapping clothing. Long hair can also get caught;
Practical jokes and horseplay;
Removing protective guards on machinery, “because they get in the way”;
Operating dangerous machinery while under the influence of alcohol or medication;
Welding among a clutter of flammable material.
The causes of major injuries are much the same as minor ones. The severity is a matter of chance, so it makes sense to avoid all accidents.
Disability
Disability is the major cause of personnel losses. The frequency of disability is a good deal higher than the death rate. Apart from accidents, there are less obvious kinds of disability. Chronic, latent or developing physical conditions – back problems, repetitive stress injury, exposure to harmful physical environments, mental stress, – tend to be ignored until they become severe. When they are not recognised, their present costs are ignored and their future costs accumulate.
Perform an analysis to rate the impact of each scenario
Once the risk has been identified, you need to assess each item in order to determine the extent of the risk in terms of its potential impact on the individual and/or the company.
This is done by analysing each item identified according to whether it is a high, medium or low risk to the business. You will have to use set criteria, i.e. a list of what low, medium, or high risk will mean.
Examples:
If you are not complying with a procedure and it will result in placing people’s lives in danger, then your action would be rated as a high risk.
If non-compliance to a procedure will result in wasted time of 15 minutes, then you would probably rate it as a low risk
Rating Risks
Risk is rated on a three-tiered scale according to the impact that the action would have on the employee and/or the organisation:
Low risk
Medium risk
High risk
Part of this process of assessing risks is to assess the likelihood of any risk materialising.
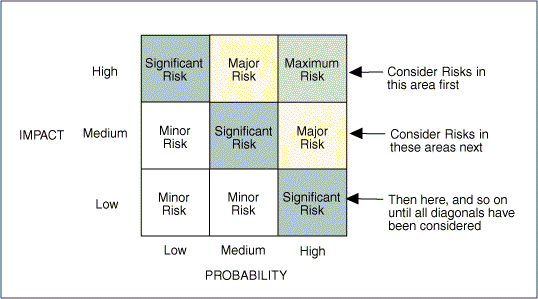
The impact of the risk can be mapped on a graph:
For example, there is a risk that someone will die of natural causes at a promotional event that you organise. The likelihood of this occurrence will depend on the type of event. At an event for old age pensioners it is a possibility. The effect on the event can be very large. The event manager will have to virtually drop what she is doing and immediately attend to this situation. For most events this risk will be high on the left- hand side of the graph.
Evaluating risks and prioritising risks:
The next step is to evaluate the risk arising from each hazard. This can be done by considering:
how likely it is that a hazard will cause harm (e.g. whether it is improbable, possible but not very likely, probable, or inevitable over time)
how serious that harm is likely to be (e.g. resulting in minor damage, a non-injury incident, a minor injury (bruise, laceration), a serious injury (fracture, amputation, chronic ill-health), a fatality, or a multiple-fatality)
how often (and how many) workers are exposed.
A straightforward process based on judgement and requiring no specialist skills or complicated techniques could be sufficient for many workplace hazards or activities. These include activities with hazards of low concern, or workplaces where risks are well-known, or readily identified and where a means of control is readily available.
In some other cases it may not be possible to identify the hazards and evaluate risks without professional knowledge, support and advice. This may arise in respect of the more complex processes and technologies in the workplace, or hazards, such as those related to health, which may not be readily or easily identifiable, and may require analysis and measurements.
Risk Estimation
Risk estimation can be quantitative, semi-quantitative, or qualitative in terms of the probability of occurrence and the possible consequence.
For example, consequences both in terms of threats (downside risks) and opportunities (upside risks) may be high, medium or low (see below). Probability may be high, medium or low but requires different definitions in respect of threats and opportunities (see tables that follow).
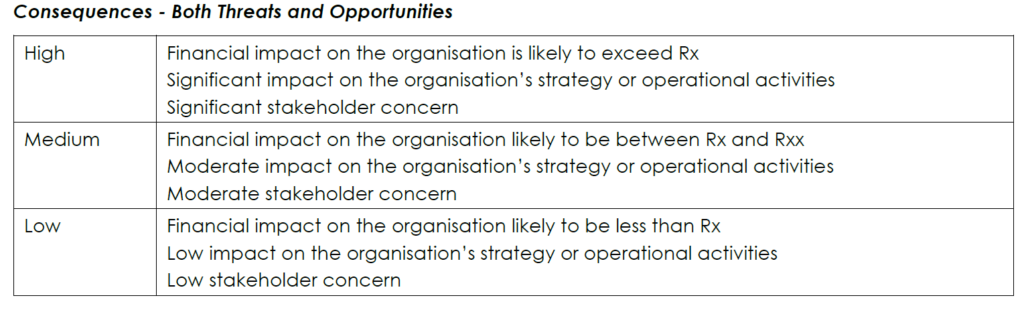
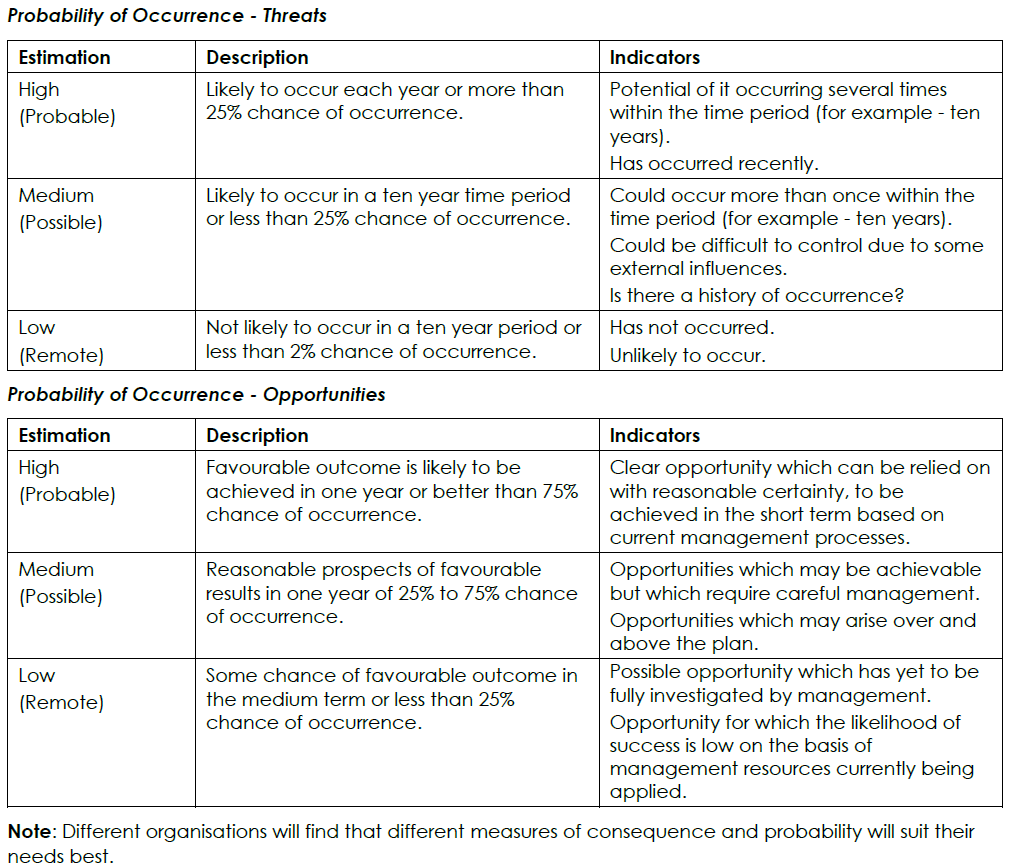
For example many organisations find that assessing consequence and probability as high, medium or low is quite adequate for their needs and can be presented as a 3 x 3 matrix. Other organisations find that assessing consequence and probability using a 5 x 5 matrix gives them a better evaluation.
Authenticating Sources of Information
Ensure that the risks associated with acting on, or repeating unverified and unsubstantiated information, are identified / known. Should you be in doubt over anything, you need to authenticate the sources of information, or consult with a trusted source, such as your supervisor or a person with more experience.
Should you act on or repeat unverified and unsubstantiated information, chances are that you could be wrong and that you are undertaking a high risk action. Taking such high risks is never recommended and therefore it is of utmost importance that you ensure that the information that you use to assess the risk:
Can be trusted
Is authentic
Has been verified
Is substantiated with proof
Sources of Information:
People
Documentation – Financial documents are an excellent source of information for risk identification. Budget forecasts and financial statements provide a good indication of the company’s overall position. These documents can assist in defining resource flows, physical and capital assets and events and activities that may affect future budgets.
Observation – Observing people doing their work or on-site inspections are another source of information for risk identification. For example, company reports indicate that production has declined at one of your facilities. An on-site visit to the facility reveals that production could be increased if a machine that is no longer in use could be put back into operation.
Statistical Analysis – Statistical analysis can help identify areas of risk, such as worker injuries and employee benefits.
Process (procedure) or Operational Analysis – Process (procedure) or operations analysis can be used to evaluate work processes, resource flows and other operational risk sources.
Verifying sources of information:
By examining internal documents and industry-related comparative data you can pinpoint your company’s level of risk exposure and determine what issues need to be addressed to improve risk management. Additional information about the industry environment and macro environments can be obtained by reviewing newspapers, trade publications, business periodicals, and similar materials.
Information must be verified and substantiated as decisions to ensure the welfare of the organisation and its people are taken based on the information gathered. If this information is incorrect it could have detrimental results for the organisation. To minimise the risk of acting on unverified information, the information must be verified, e.g. financial information verified by an external auditor.
When dealing with risk assessment, it is important to understand probability.
Probability Theory
Probability applications are meant to make dealing with uncertainty more rational, rather than depending on ‘gut-feel’ intuition and hunches.
“The theory of probability is at bottom only common sense reduced to calculation”.47
Definition: The probability of an event is a measurement of the chance that the event will occur within a given time period.
Probability can be expressed as a number that varies between 0 and 1.
0 = the event cannot occur
1 = the event is certain to occur
Values in between can be expressed as fractions (1/2; 1/1000) decimals, (0,5; 0,001) or percentages (50%; 0,1%). The closer the probability to 1,0 (or 100%), the more likely the event becomes.
There are two possible approaches to determining probability:
A Priori
A Posteriori
A Priori
This is based on facts which are evident at the beginning (Prior – first).
There are a known number of outcomes
o Each outcome has a probability which is known, or can be precisely calculated.
Example 1
In the toss of a coin, the probability of this landing with the “head” up is ½ because:
There are two equally possible outcomes – a head or a tail;
one of these two represents the event being determined.
Example 2
In the same way, the probability of drawing an ace from a well-shuffled deck of cards is 1/13 because out of 52 cards there are four aces.
This is interesting, but not much use to insurers or risk managers. A business with 52 warehouses does not know for certain that only 4 can have fires or thefts.
A Posteriori
Probabilities are based on past experience (Posterior = back). This is sometimes known as the statistical probability, because the true probability is estimated from the observed number of exposures and previous occurrences.
Example 1
If a fast-food chain had 10 000 identical hotdog stalls throughout the country and 200 were damaged by fire in one year, they might assume that the probability of fire in one of their stands was 200/10 000 or 1/50.
Example 2
In a fleet of 100 similar vehicles, 25 are damaged in accidents. The probability is 1/4.
The Law of Large Numbers
The larger the number of similar exposure units, the more accurately you can predict the probability that a particular unit will suffer loss.
If the fast-food chain had only 100 stands instead of 10 000, and 2 sustained loss, the calculated probability would be the same, 1/50. However, there would be less confidence in how close this would come to the real probability of loss. The proportion of stalls that suffer loss could fluctuate widely from year to year.
Probability can be interpreted as the proportion of times a specified event will almost certainly occur out of a large number of trials.
Temporal and Spatial Interpretation
The temporal interpretation emphasises the proportion of times a loss will occur to a given number of units in the long run (how often, over a long period of time);
The spatial interpretation emphasises the proportion of similar units that will suffer loss during a given period (how many over a given time period).
Examples
Each car exposed next week;
Each warehouse exposed next year;
Each shipment exposed next month.
This is the proportion that can be expected on the average over many units. No one knows what will happen to any particular unit.
Application
A firm makes 1 000 shipments a year; for each of these, the probability of theft is 1/10; knowing that about 10 percent will be lost indicates the size of the exposure; it is also possible to measure the benefit of reducing the chance of loss to say, 1/20, or transferring the exposure to some other party.
The Multiplication Rule (First Law of Probability)
Suppose that four shipments are made to the same four customers, ABC and D, every month. From past statistics, the spatial interpretation shows the probability of theft of any one of the four shipments to be 1/4. The risk manager feels that this risk can profitably be retained – the insurance premium would be more than the normal loss expectancy. However, the maximum foreseeable loss is that of all four shipments. What is the probability of this, and how much will he be prepared to pay for insurance cover?
The first law of probability states:
The probability that two or more independent exposure units will suffer a loss is equal to the product of the probabilities of loss for each of these units.
More simply, this is called the Multiplication Rule.
In our example, if the probability of each unit being involved is 1/4, then
Two units 1/4 x 1/4 = 1/16
Three units 1/4 x 1/4 x 1/4 = 1/64
Four units 1/4 x 1/4 x 1/4 x 1/4 = 1/256
On this basis, it may be possible to negotiate a reasonable rate of premium, based on excluding the first, or the first two losses in any one month.
Formula
Shortening Probability to ‘P’ and calling the units A, B, C and D, this could be written as:
P (A and B) = P(A) x P(B)
P (A, B and C) = P(A) x P(B) x P(C), and so on.
Application
Now think of two buildings, A and B. A is a woodworking shop, with a probability of fire of 0,05.
B is a metal worker, where the probability is 0,02. The buildings are so close together that if one catches fire, there is an 85% chance (0,85) that the other will burn as well.
P(A) = 0,05
P(B) = 0,02
P(A/B) or (B/A) = 0,85
P(A and B) = P(A) P(B/A)
= (0,05) (0,85)
= 0,0425 or about 1/24
Notice that this is the probability if building A starts the fire and spreads it to building B – probability (A and B).
There is a lesser probability that B is first to catch fire (B and A)
P(B and A) = P(B) x P(A/B)
= (0,02) (0,85)
= 0,017 or nearly 1/60.
Additions Rule
In the above examples, there are two probabilities – the event will, or will not occur. Because the figure 1 represents certainty, the sum or total of all the alternatives must equal one.
If the probability of a car accident is 1/4, the probability of no accident is 3/4.
If the probability of a building having a fire is 0,05, the probability of it not having one is 0,95.
Probability Trees
We can use this fact in drawing up a probability tree, which is a useful way of illustrating how events combine.
Example 1
At a particular site, the likelihood of a theft occurring is 0,2.
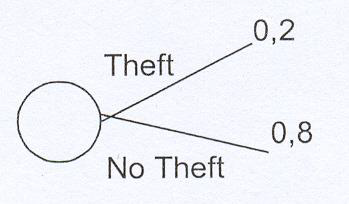
The respective probabilities are shown at the tips of the branches.
Example 2
Now we might think about the kind of theft. It might involve:
Fixtures and fittings 0,3 probability
Stock 0,5 probability
Plant 0,2 probability
Notice again, that these add up to 1, being the total of all the probabilities.
Example 3
We said that the overall likelihood of a theft was 0,02, we can now split this figure as to fixtures, stock or plant
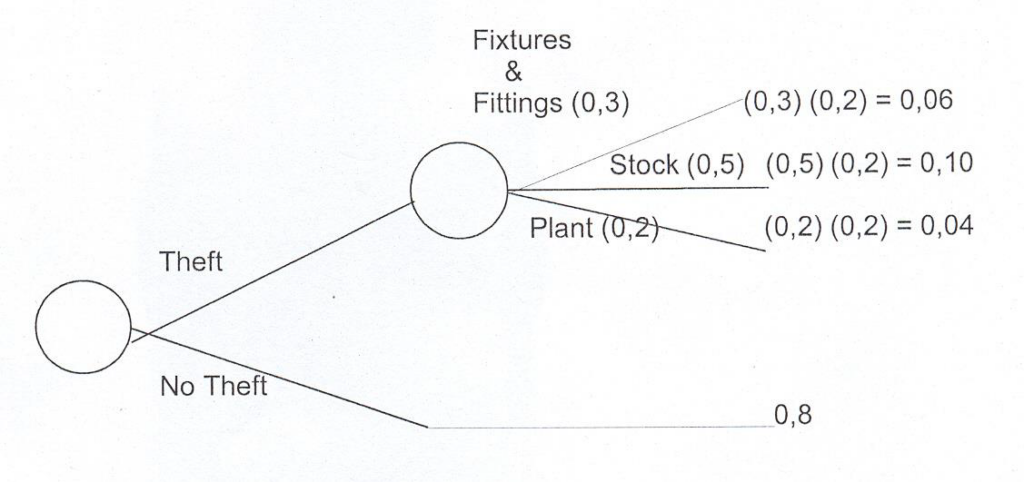
In each case – fixtures, stock, plant, the loss might be large, or small.
The Prouty Approach
This straightforward non-mathematical approach identifies four broad categories of loss frequency
Almost nil – extremely unlikely
Slight – has not happened, but could happen
Moderate – happens once in a while
Definite – happens regularly.
There are also three categories of loss severity:
1 Slight – the organisation can readily retain each loss
2 Significant – the organisation cannot retain the whole of the loss, some part must be transferred
3 Severe – virtually all of the loss must be transferred or the survival of the organisation is endangered.
1, 2 and 3 above will vary with the size of the organisation and its financial resources.
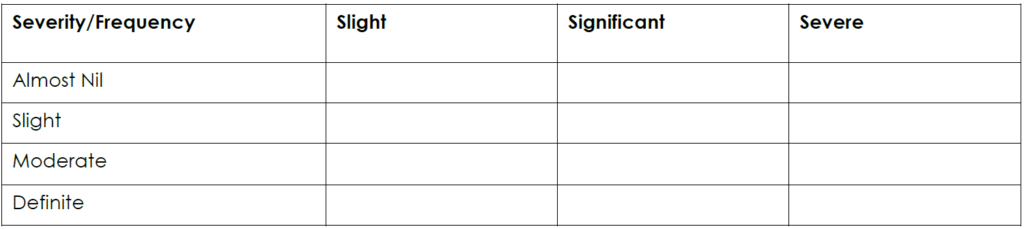
These broad categories can be readily understood, but the financial significance must then be inferred, which brings us back to the need for some kind of mathematical basis.
Practical Application of Probability Theory
It is useful to be able to back up your arguments with figures.
Example:
Stock is valued at R200 000. A total loss is possible.
The probability of theft is 0,1 in any one year. Would it be worth spending, say R24 000 on theft insurance?
Might you consider spending R10 000 on improved security, and carry the risk yourself? (The answer depends on the management style of your company. Although the probabilities favour retaining the risk, management may be unwilling to run the risk of losing R200 000).
If petty theft from your offices is costing the company R4 000 a year, could you justify installing a new security system costing R20 000? (What is the useful life and maintenance cost of the system? Will it continue to save money over a number of years?)
Probability vs. Possibility
Possibility is a binary condition – either something is possible, or it’s not – 100% or 0%.
Probability reflects the continuum between absolute certainty and impossibility.
The simple fact is that risk is always a probability issue.
Consider the difference between playing Russian roulette with a standard six-cylinder revolver versus a semi-automatic.
The possibilities are equal with either handgun – i.e., it’s 100% possible in both cases that the player would suffer a “negative outcome.”
The probabilities, however, are significantly different:
o In the first case, assuming the revolver is loaded with a single bullet, the probability of a negative outcome is about 17%.
o In the second case, assuming a single bullet is loaded and chambered in the semi-automatic, the probability of a negative outcome is about 100% (it might, of course, misfire). Clearly, you would rather not play the game at all, but if you had to choose between the two weapons, you would much rather base your choice on an understanding of the probabilities, as opposed to just the possibilities.
Decision-makers want and need the benefit of this same quality of information, when dealing with risk assessments.
Risk Profile
The result of the risk analysis process can be used to produce a risk profile which gives a significance rating to each risk and provides a tool for prioritising risk treatment efforts. This ranks each identified risk so as to give a view of the relative importance.
This process allows the risk to be mapped to the business area affected, describes the primary control procedures in place and indicates areas where the level of risk control investment might be increased, decreased or reapportioned.
Accountability helps to ensure that ‘ownership’ of the risk is recognised and the appropriate management resource allocated.
Risk Evaluation
When the risk analysis process has been completed, it is necessary to compare the estimated risks against risk criteria which the organisation has established. The risk criteria may include associated costs and benefits, legal requirements, socioeconomic and environmental factors, concerns of stakeholders, etc.
Risk evaluation, therefore, is used to make decisions about the significance of risks to the organisation and whether each specific risk should be accepted or treated.
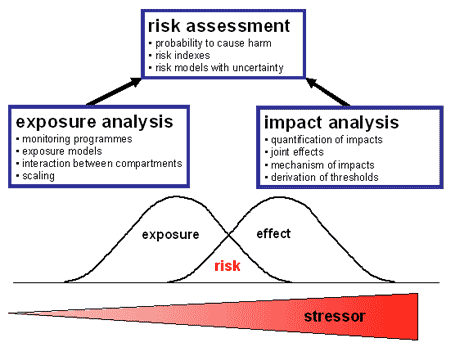
Example risk assessment for an office-based business
This example risk assessment shows the kind of approach a small business might take. It can be used as a guide to think through some of the hazards in your workplace and the steps you need to take to control the risks. Please note that it is not a generic risk assessment that you can just put your company name on and adopt wholesale without any thought. This would not satisfy the law – and would not be effective in protecting people.
Every business is different – you need to think through the hazards and controls required in your workplace for yourself.
Setting the scene
The office manager carried out the risk assessment at this company, which provides management and financial consultancy services, and which leases two storeys of a ten-storey office block.
Eighteen staff work at the company, one is a wheelchair user. The offices contain typical office furniture and equipment. There is a staff kitchen, where drinks can be prepared and food heated, and toilet and washing facilities on each floor.
The offices are cleaned every evening by cleaners from a general office cleaning contractors. They store the cleaning materials in a locked cupboard.
The office block was built before 2000. The landlord has surveyed the building for the presence of asbestos and has shared the findings of this survey with all of the tenants. Asbestos-containing materials (ACMs) were found but were in good condition and in places they were not likely to be damaged, worked on or disturbed, so it was decided to leave them in place.
The office block is locked from 9:00 pm to 6:00 am Monday to Friday and at weekends, although 24 hour/7 days a week security cover is provided.
Although this example risk assessment is for an office-based business, it may equally be applied to any business that has office-based functions within it.
How was the risk assessment done?
The manager followed the guidance in Five steps to risk assessment.
- To identify the hazards, the manager:
looked at company’s office health and safety intranet pages, to learn where hazards can occur, and at the disability and risk assessment web pages;
walked around the office, noting things that might pose a risk and taking into consideration what was learnt from the health and safety guidance;
talked to supervisors and staff, including the member of staff who is a wheelchair user, to learn from their knowledge and experience of areas and activities, and listen to their concerns and opinions about health and safety issues in the workplace;
talked to the office cleaning contractors, to ensure that the cleaning activities did not pose a risk to office staff, and vice-versa;
looked at the accident book, to understand what has previously resulted in incidents. - The manager then wrote down who could be harmed by the hazards and how.
- For each hazard, the manager wrote down what controls, if any, were in place to manage these hazards. The manager then compared these controls to the good practice guidance provided in HSE’s office health and safety web pages. Where existing controls were not considered good enough, the manager wrote down what else needed to be done to control the risk.
- Putting the risk assessment into practice, the manager decided and recorded who was responsible for implementing the further actions and when they should be done. When each action was completed, it was ticked off and the date recorded. The manager pinned the risk assessment up in the staff room for all staff to see.
- At an office meeting, the office manager discussed the findings with the staff and gave out copies of the risk assessment. The manager decided to review and update the risk assessment every year, or straightaway if any major changes in the workplace happened. 48
Develop contingency plans for managing risk
There are many cases of relatively small property losses resulting in prolonged stoppages of production. That is why contingency planning is so important.
Contingency planning is a kind of back-up, or safety net, to the risk management process.
Deciding on preventive action:
Having evaluated the risks, the next step is to put in place preventive and protective measures. Among the things to be considered at this stage are:
Whether risks are preventable or avoidable. Is it possible to get rid of the risk? This can be done, for instance, by:
considering whether the task or job is necessary,
removing the hazard,
using different substances or work processes.
- If risks are not avoidable or preventable, how risks could be reduced to a level at which the health and safety of those exposed is not compromised. When determining a strategy to reduce and control risks, employers should be made aware of the following additional general principles of prevention:
combating the risk at source
adapting the work to the individual, especially as regards the design of workplaces, the choice of work equipment and the choice of working and production methods, with a view, in particular, to alleviating monotonous work and work at a predetermined work-rate and to reducing their effect on health
adapting to technical progress
substituting the dangerous by the non-dangerous or the less dangerous (replacing the machine or material or other feature that introduces the hazard by an alternative)
developing a coherent overall prevention policy which covers technology, organisation of work, working conditions, social relationships and the influence of factors related to the working environment
giving collective protective measures priority over individual protective measures (e.g. controlling exposure to fumes through local exhaust ventilation rather than personal respirators)
giving appropriate instruction to workers.
For guidance on the control of risk through these measures employers should be referred to specifications, in national legislation, national standards, published guidance and other such criteria, published by national authorities.
A further important general principle of which employers need to be aware is that they should not transfer risks. That is to say that in providing a solution to one problem, another problem should not be created. For instance, it would be of doubtful benefit to provide double-glazing to office windows in order to reduce noise from outside, unless provision was made for adequate ventilation.
Contingency Strategies for managing risk
Once risks have been identified and assessed, all techniques to manage the risk fall into one or more of these four major categories:
Avoidance
Reduction / Mitigation / Modification
Acceptance / Retention
Sharing / Transfer
Ideal use of these strategies may not be possible. Some of them may involve trade-offs that are not acceptable to the organisation or person making the risk management decisions.
Avoidance
Avoidance includes not performing an activity that could carry risk. An example would be not buying a property or business in order to not take on the liability that comes with it. Another would be not flying in order to not take the risk that the aeroplane could be hijacked.
Avoidance may seem the answer to all risks, but avoiding risks also means losing out on the potential gain that accepting (retaining) the risk may have allowed. Not entering a business to avoid the risk of loss also avoids the possibility of earning the profits.
Whenever an organisation cannot offer a service while simultaneously ensuring a high degree of safety, it should choose avoidance as a risk management technique. Do not offer programs/ services/ products that pose too great a risk. In some cases avoidance is the most appropriate technique if an organisation simply doesn’t have the financial resources required to fund adequate training, supervision, equipment, or other safety measures. Always ask, “Is there something we could do to deliver this program/conduct this activity safely?” If you answer “yes,” risk modification may be the more practical technique.
Reduction/ Mitigation/ Modification
Modification involves methods that reduce the severity of the loss. Examples include sprinklers designed to put out a fire to reduce the risk of loss by fire. This method may cause a greater loss by water damage and therefore may not be suitable. Alternative fire suppression systems may mitigate that risk, but the cost may be prohibitive as a strategy.
Modification is simply changing an activity to make it safer for all involved.
Policies and procedures are examples of risk modification. An organisation concerned about the risk of using unsafe drivers may add licence checks to its screening process, or an annual road test for all drivers.
Acceptance / Retention
Retention involves accepting the loss when it occurs. True self-insurance falls in this category. Risk retention is a viable strategy for small risks where the cost of insuring against the risk would be greater over time than the total losses sustained.
All risks that are not avoided or transferred are retained by default. This includes risks that are so large or catastrophic that they either cannot be insured against, or the premiums would be prohibitive. War is an example since most property and risks are not insured against war, so the loss attributed by war is retained by the insured. Also any amounts of potential loss (risk) over the amount insured is retained risk. This may also be acceptable if the chance of a very large loss is small or if the cost to insure for greater coverage is so great it would hinder the goals of the organisation too much.
There are two ways to retain risk. The first is by design. Organisations make conscious decisions to retain risk every day. For example, when an organisation purchases liability insurance and elects a certain excess amount, it’s retaining risk. This can be a rational and appropriate approach to managing risk.
Where organisations get into trouble is when risk is retained unintentionally. The unintentional retention of risk can be the result of failing to understand the exclusions of an insurance policy, insufficient understanding of the scope of risk the organisation faces, or simply because no one has taken the time to consider the risk and how it can be addressed.
Sharing / Transfer
Sharing or risk transfer means causing another party to accept the risk, typically by contract or by hedging.
Risk sharing can therefore involve sharing risk with another organisation through a contract. Two common examples are insurance contracts that require an insurer to pay for claims expenses and losses under certain circumstances, and service contracts whereby a provider (such as a transportation service or caterer) agrees to perform a service and assume liability for potential harm occurring in the delivery of the service.
Risk retention pools are another way of retaining risk for a group. Unlike traditional insurance, no premium is exchanged between members of the group up front, but instead losses are assessed to all members of the group.
Applying Contingencies
Shamsher Haider, a PMI certified project management professional (PMP) suggests the following on the ERPM blogspot:
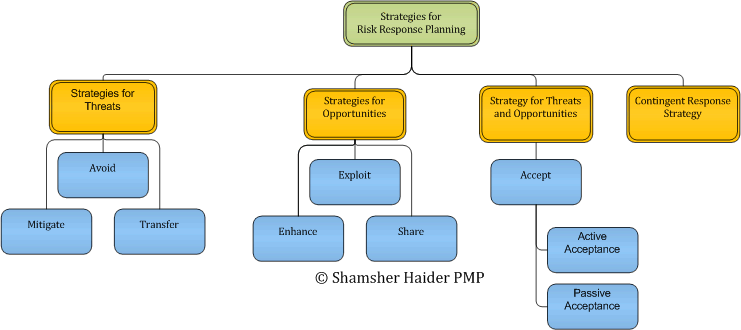
Strategies for Threats:
Avoid: This means staying clear of the risk altogether. While avoidance obviously is the best possible course, it might not be feasible in all circumstances, e.g. the impact of the cost of avoidance might dominate the benefits of avoiding the risk. Avoidance can be accomplished by changing the process or the resources to attain an objective or sometimes modifying the objective itself to avoid the risks involved. An example of avoiding risk could be avoiding use of untested third party components in the software design, or avoiding inclusion of an inexperienced resource in the project team.
Mitigate: This means trying to reduce the probability and/or impact of the risk. Reduction in probability of occurrence would reduce the likelihood of its occurrence and reduction in impact would imply a lesser loss if the risk event occurs. 100% mitigation would be equivalent to avoidance. An example of mitigation would be an early verification of the requirements by prototyping before moving on to full-fledged development.
Transfer: This implies transferring the liability of risk to a third party. While this strategy does not eliminate or mitigate the risk or its consequences itself, it transfers the responsibility of its management to someone else. Insurance is a classic example of this strategy. By buying insurance you transfer your risk to the insurance company by paying the risk premium. Fixed Cost contract is yet another example of risk transfer strategy. In a fixed cost contract the risk is transferred to the seller.
Strategies for Opportunities:
Exploit: This strategy involves removing all uncertainties pertaining to a positive risk and making sure that the risk event occurs. An example could be a situation where the seller will pay an incentive fee if work is completed a week ahead of the completion deadline. Ordinarily there is a probability that the work might get completed earlier, but if we plan to exploit this situation, we will plan to complete the work a week ahead to turn this uncertainty into a certain event.
Enhance: This strategy involves planning for increasing the size of the opportunity by increasing its impact and /or the probability of its occurrence. Identification of the root cause of the presence of an opportunity can help focus on the root cause and enhance its impact and / or probability.
Share: This strategy involves sharing the fruits of an opportunity with a third party because you do not have the capability to exploit it alone. Suppose your competitor is set to launch a new product six months from now, and you identify the opportunity that by launching a product with similar features a month before your competitor’s launch you can wrest the market away. In this particular scenario the situation becomes complicated because you have all the resources to launch your product in five months except a portion requiring device driver and hardware level programming. You can launch a joint venture with another company specialising in device driver programming to share the opportunity.
Strategy for Threats and Opportunities:
Accept: Sometimes we identify a risk but realise that time and / or resources required to formulate and enact response strategies overweigh the results of the effort. In such a case we just accept the risk. If we plan to face the occurrence as it is, it is called passive acceptance. On the other hand if we develop a contingency reserve to handle the situation if the risk occurs, we call it active acceptance.
Contingent Response Strategy:
Also known as contingency planning, this strategy involves development of alternatives to deal with the situation after the risk has occurred. Active acceptance of risks leads to contingency planning, whereby we anticipate a risk to occur and instead of trying to mitigate or eliminate its occurrence we plan what to do when the event occurs. Contingency reserves are a commonly used tool to handle the occurrence of a risk event. Contingency reserve can imply allocation of cash, time or resources to cope with the situation when the risk event has occurred.
Fallback plans can be developed for high impact risks. A fallback plan as the name suggests, is the backup plan, in case the original contingency plan doesn’t work out as planned. An example could be identification of risk that a certain .Net programmer will resign in middle of the project. Since under the current circumstances you can do nothing to mitigate or eliminate the risk you accept it but develop a contingency plan to hire a certain programmer on hourly wages. To cope with the situation if no programmer is available on hourly wages at the time of resignation of your programmer, you develop a fall back plan of temporarily moving a software engineer from a certain low priority project to work on the assignment till an alternative can be hired.
Develop Contingency Plans in Accordance with Organisational Policies and Procedures
After the most appropriate preventive and protective measures have been identified, the next step is to put them in place effectively.
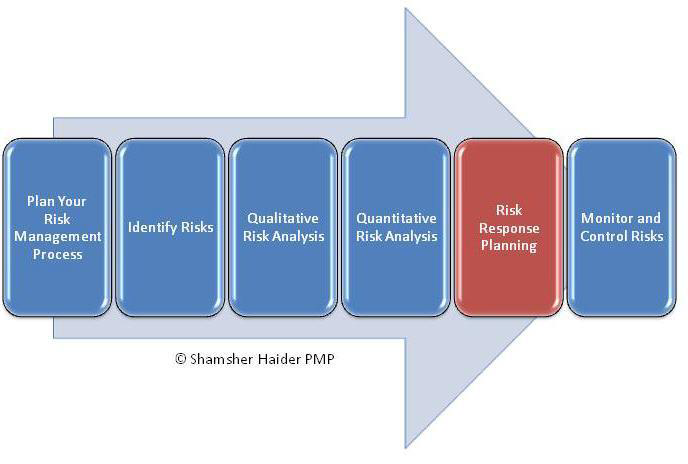
Effective implementation involves the development of a plan specifying:
the measures to be implemented
the means allocated (time, expenses, etc.)
who does what and when
when actions are to be completed, and
a date for reviewing the control measures.
It is important to involve workers and their representatives in the process:
to inform them about the measures implemented, about how they will be implemented, and who will the person in charge of implementing them
to train or instruct them about the measures or procedures that will be implemented.
In preparing a contingency plan to deal with the interruptions to the organisation’s business, the first steps should be to identify:
All potential sources of loss-producing events which may disrupt operations;
Interdependences between different parts of the organisation itself; for example, would damage to one process or storage area disrupt all production of one or more of a firm’s products?
Dependencies upon individual suppliers or customers;
Alternative sources of supply or outlets where any of the above dependencies exist;
All seasonal factors.
Steps to develop the Contingency Plan
Step 1: Risk Management Planning – The manager and the team decide who is going to develop the risk management plan
Step 2: Risk Identification – The assigned team identify the various risks and make a list of the risks through brainstorming, interviewing and sample risk lists.
Step 3: Risk Probability – The risk management plan team, determine the probability of the risks occurring through Impact Scales.
Step 4: Risk Response Plan – The risk management plan team decides for each identified risk whether to accept the risk, avoid the risk or accept the risk.
Step 5: Risk Monitoring and Control – Risk monitoring and control is a process that lasts the entirety of the project. The team monitors the risks as the project matures, new risks develop and anticipated risks disappear.
The contingency plan should specify the responses to each of the different types of loss situations, setting out the steps to be followed under various circumstances and assigning responsibilities for various tasks:
- List every business process in the department. (Example: Payroll might be listed in the Human Resource’s plan.)
- List the tasks for every business process and the steps it takes to complete these tasks.
- For every step, list every dependency (computer hardware, software, external and internal suppliers.)
- Rate the likelihood for each dependency to fail (Prioritise! Usually a 1-High, 2-Medium or 3-Low works well. Alphabetising with H, M or L usually doesn’t work as well, because these three letters – alphabetically – don’t follow your priority. Remember this when you design your database! )
Assume that every dependency will fail, beginning with 1-High dependencies.
- Write a contingency action that accomplishes the task without relying upon the dependency.
Once you have analysed business functions this way, you will be able to create contingencies at the appropriate places. In many areas, the contingency will be at the task level; in other areas at the process level; still others may be at the department level.
In some cases, no viable contingency is possible. If the power goes down, and you have no generator, you aren’t doing any business. If this is the situation with any specific process, make a note of it and describe what you’ll do if the dependency fails.
Structure your contingency plan positively – involve the appropriate people and the right numberof people – it’s a big task, after all. It will require input from many.
Ongoing Training
Any disaster and crisis management plans must be tested regularly and updated where shortcomings are found so that the plans are not only kept as up-to-date as possible, but also so that the personnel involved have been trained.
Crisis Situations
It must be realised that having a plan, even if it is kept up-to-date and even if people have been fully trained in what to do, will not necessarily result in your being able to cope with the crisis when it occurs. It is essential for those who are drafting or amending the plan to bear in mind that:
The more severe the crisis is, the greater the loss of or lack of resources
The plan will not work without people to make it come alive
The effects of stress on both people and the plan will be unpredictable. The plan as a consequence will work in unpredictable ways
Communicate Contingency Plans to relevant Stakeholders
Key to the success of the risk management process is communication and consultation with key staff. Staff members will assist in the identification process, as well as treating and monitoring the risks. They will have a part in putting together the risk management plan, and can be assigned to oversee certain risks that may impact on their area of the business.
Wide consultation will help ensure that most risks are identified, helping to lessen the potential of things going wrong.
The human factor is rarely absent from risk situations. Frequently carelessness, incompetence or lack of technical knowledge is either the primary or at least a contributory cause of a loss-producing event. Furthermore, the failure of an individual or group to respond in the correct way to a loss situation may contribute to the size of the ensuing loss. Consequently training and effective communication have a major role to play in loss reduction programmes and should cover everyone employed by, or associated with the work of an organisation.

Management
The aim should be to create in management an awareness of the risks to which the organisation is exposed and of the ways in which they may be controlled. The lead in risk control, and therefore loss control, must come from top management, and, although only a few members of the top management team will need to have a detailed technical knowledge of the various risks and hazards, all should understand and have a commitment to the principle of total risk control. Risk control is essential at every stage of an organisation’s activities such as:
At the planning stage;
At the production stage;
After sales usage and service.
Staff
There are several fundamental points to bear in mind when communicating the contingency plans to employees:
They need to be aware of the hazards to which they may be exposed in the course of their work and what steps they can take to minimise the risk of injury to themselves and fellow employees;
Training may be required regarding the use of special clothing and equipment provided for their safety;
Instructions for all employees as to what to do in emergencies, for example, upon the outbreak of fire, breakdown of plant, and especially the breakdown of safety devices;
Training of some employees to deal with emergencies until expert help arrives, for example the training of first-aid and firefighting teams;
Installing a sense of safety-consciousness in all employees, both in relation to the way they carry out their work and in the avoidance of defects in the firm’s products. Each employee should feel a sense of responsibility towards fellow-employees, customers and the general public.
Contractors, Suppliers and Servicing Agents
Sometimes the organisation can be jeopardised by people other than its own employees:
Contractors and sub-contractors who undertake work on its behalf;
Suppliers of components and raw materials.
All these people should be made aware of the risks that affect the organisation, and their cooperation sought. For example, is it fair to blame a welder who accidentally starts a fire, if the area where he is
working was not first cleared of flammable materials?
Expensive mechanical failures and products recall have resulted from minor impurities in lubricants and raw materials.
Risk Reporting and Communication
Internal Reporting
Different levels within an organisation need different information from the risk management process.
The Board of Directors should:
know about the most significant risks facing the organisation
know the possible effects on shareholder value of deviations to expected performance ranges
ensure appropriate levels of awareness throughout the organisation
know how the organisation will manage a crisis
know the importance of stakeholder confidence in the organisation
know how to manage communications with the investment community where applicable
be assured that the risk management process is working effectively
publish a clear risk management policy covering risk management philosophy and responsibilities.
Business Units should:
be aware of risks which fall into their area of responsibility, the possible impacts these may have on other areas and the consequences other areas may have on them
have performance indicators which allow them to monitor the key business and financial activities, progress towards objectives and identify developments which require intervention (e.g. forecasts and budgets)
have systems which communicate variances in budgets and forecasts at appropriate frequency to allow action to be taken
report systematically and promptly to senior management any perceived new risks or failures of existing control measures.
Individuals should:
understand their accountability for individual risks
understand how they can enable continuous improvement of risk management response
understand that risk management and risk awareness are a key part of the organisation’s culture
report systematically and promptly to senior management any perceived new risks or failures of existing control measures.
External Reporting
A company needs to report to its stakeholders on a regular basis, setting out its risk management policies and the effectiveness in achieving its objectives.
Increasingly stakeholders look to organisations to provide evidence of effective management of the organisation’s non-financial performance in such areas as community affairs, human rights, employment practices, health and safety and the environment.49
Good corporate governance requires that companies adopt a methodical approach to risk management which:
protects the interests of their stakeholders
ensures that the Board of Directors discharges its duties to direct strategy, build value and monitor performance of the organisation
ensures that management controls are in place and are performing adequately.
The arrangements for the formal reporting of risk management should be clearly stated and be available to the stakeholders.
The formal reporting should address:
the control methods – particularly management responsibilities for risk management
the processes used to identify risks and how they are addressed by the risk management systems
the primary control systems in place to manage significant risks
the monitoring and review system in place.
Any significant deficiencies uncovered by the system, or in the system itself, should be reported together with the steps taken to deal with them.
Distribute and store Contingency Plans
Your contingency plans must be distributed and stored in accordance with the organisation’s risk management procedures.
Some recommendations are:
Formally review and update the plan at least quarterly.
Review contingencies within the plan, such as storage of a specific set of records, and update the contingencies on a regular schedule. The frequency of updating will vary with the degree the material changes over time and the degree of risk the firm accepts if the data is outdated.
Store disks or tapes of critical information such as accounts receivable, client information, vendor and personnel records or outstanding billings in a safe, secure place such as a bank vault.
Duplicate prepared information and place in a three-ring binder to facilitate adding and deleting materials over time.
Maintain duplicate records at a different site
Individuals with key responsibilities should keep copies of the emergency plan at their homes
TEST AND REVISE CONTINGENCY PLANS
After you have prepared the contingency plan, you need to do several things to keep it practical and relevant – don’t just create a document and file it away. As your business and its environment change, you’ll need to review and update these plans accordingly.
Here are some key steps in the contingency plan maintenance process50: Communicate the plan to everyone in the organisation. Inform people of their roles and responsibilities related to the plan. Provide necessary training for people to fulfil these roles and responsibilities. Conduct disaster drills where practical.
Assess the results of training and drills, and make any necessary changes. Review the plan on a regular basis, especially if there are relevant technological, operational, and personnel changes. Distribute revised plans throughout the company, and make sure the old plan is discarded. Audit the plan periodically:
o Reassess the risks to the business.
o Analyse efforts to control risk by comparing actual performance to the performance level described in the contingency plan.
o Recommend and make changes, if necessary.
Test Contingency Plans51 Testing every contingency in your plan is time- and cost-prohibitive. To make testing manageable, test in four stages. Each stage should build on the results of the previous stage. If an area proves to be unsound, or if it conflicts with other contingency plans, you can re-write and re-test the plan. Stage 1 – Senior Staff Review The senior staff select an internally-publicised date and time to review all contingency plans. Aside from ensuring overall business soundness, this review also serves to recognise people who have thoughtfully completed their assignment. Knowledge of a firm date for a senior staff review will increase quality, accuracy and timeliness. Stage 2 – Interdepartmental Reviews Each department should review another department’s plans. The goal of this stage is to find bottlenecks, identify conflicts and allocate resources. If possible, departments that are “downstream” in the business process can review the plans of “upstream” departments. Stage 3 – Failures in Critical Systems This testing can be localised within departments. It involves simulating system or vendor failures. You don’t actually have to shut down critical equipment or processes – you can role-play a “what if” scenario. You can either run a “surprise” drill or plan a role-playing event for a specific time. Stage 4 – The Real Deal This testing involves short-term shutdowns in key areas. If possible, these tests should be conducted in a real-time environment. The goal, of course, is to fully test the contingency plan. Concentrate this last phase of testing only on areas that have a high business priority and a high risk for failure. By implementing testing in four stages, you can optimise your time and accomplish the goal of proving that the contingency plan is valid.
Monitoring and reviewing Arrangements for monitoring and reviewing the protective and preventive measures should be introduced following the risk assessment to ensure that the effectiveness of these measures is maintained, and the risks controlled. The information generated by monitoring activities should be used to inform the review and revision of the risk assessment.
Risk assessment should not be a once-and-for-all activity. The assessment needs to be reviewed and revised, as necessary, for a number of reasons, including: the degree of change likely in the work activity changes which might alter the perception of risk in the workplace, such as a new process, new equipment or materials, change of work organisation, and new work situations including new workshops or other premises once the new measures have been introduced following the assessment, the new working conditions should be assessed in order to review the consequences of the change. It is essential that the risk is not transferred, that is to say that in providing a solution to one problem, another problem should not be created the assessment no longer being applicable because the data or information on which it is based is no longer valid the preventive and protective measures currently in place being insufficient or no longer adequate, e.g. because new information is available regarding particular control measures as a result of the findings of an accident or “near miss” (a near miss is an unplanned event that did not result in injury, illness, or damage – but had the potential to do so).
Document Recommendations on Improvements to Contingency Plans
Copies of the contingency plan52 and all revisions need to be submitted to those staff members that are expected to respond to the different situations identified in the plan.
The contingency plan should be reviewed at least annually and updated whenever changes occur that will significantly affect the ability of your unit to respond to an emergency situation. This includes when the regulations are revised, if your unit’s contingency plan fails in an emergency, if your unit changes in a way that materially increases the potential for an emergency or there are changes in the response necessary in an emergency, if the list of emergency coordinators changes or if the list of emergency equipment changes. These revisions should be made to the plan immediately (within 24 hours).
It is recommended that a revision record be kept that includes amendment dates, revision numbers and a brief summary of the nature of the revision(s). It is also acceptable to make contingency plan changes in supporting documentation as long as this documentation is referenced in the original plan.
Capture lessons learned on the effectiveness of risk reduction measures. As plans are executed, they must be monitored to ensure that their objectives are achieved as intended. It should be recognised that, in a high-risk environment, the one thing that can be expected is that not everything will happen according to plan. What is important is that an understanding of what needs to be done develops during the planning and monitoring processes.
Check that the risk indicators are not being exceeded, and that reduction efforts are effective. At regular periods, the progress should be checked against the plan to ensure that:
Risks identified earlier are still valid, and the risk indicators have not changed
Any changes of risk significance are understood and communicated to those who need to know
Implemented responses have been effective and lessons learned are captured
The risk reduction measures can be considered a success (or if they are failing then identify new measures that need to be put into place)
Residual risks are acceptable, or are subject to continuing action on the plan; in this event the monitoring must continue
No other risks have materialised over time.
Discover the reason(s) for change in the risk status. It is, of course, possible that the risk reduction measures are not working as well as had been expected, and thus corrective action is required. If the corrective action required is significant in terms of cost and time, especially if it involves several risks (a highly likely situation), a new risk analysis may be required.
Risk management is not a complex task. If you follow the steps in this Learner Guide, you can put together a risk management plan for your unit in a short space of time.
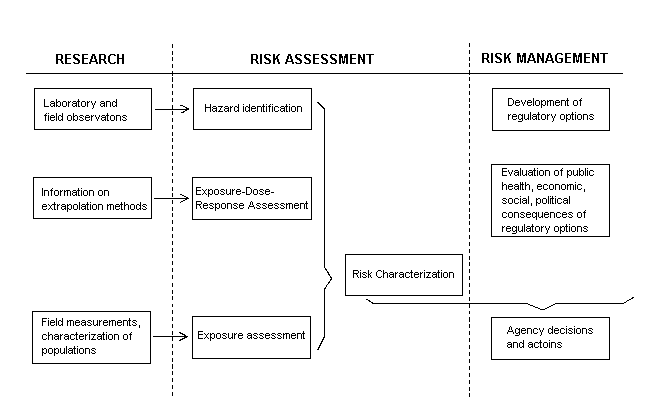
From: National Academy of Sciences / national Research council Paradigm for Research / Risk Assessment / Risk Management (NAS/NRC, 1983)
“Although we cannot foretell the future, we need to plan for it. Plan for things that could go wrong, and for things that could go exceptionally right.”
Brock Henderson
